Blog
Insights, tutorials, and best practices for network administrators and developers.
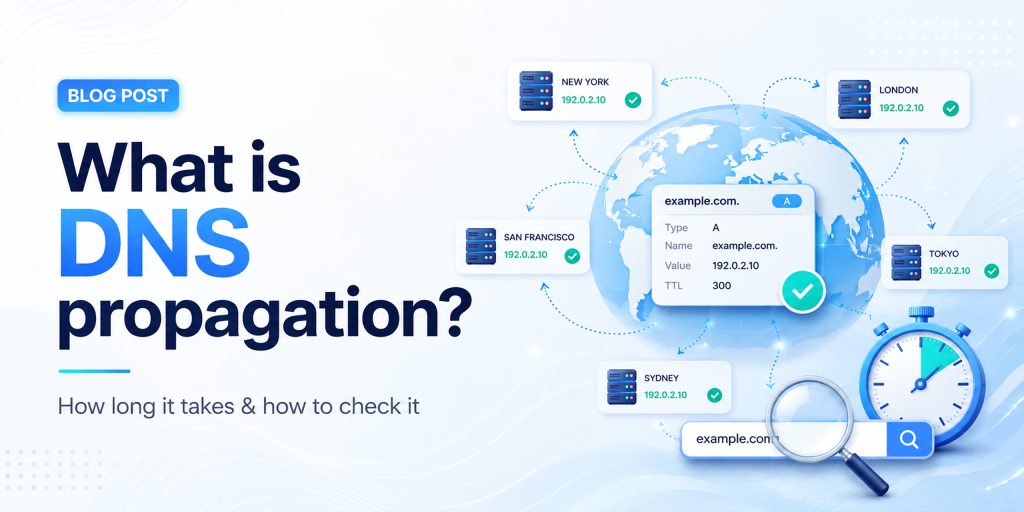
You’ve just updated your nameservers, pointed your domain to a new host, or changed a DNS record, and now you’re waiting. Your website might be showing the old version, or visitors in different countries see something different from you. This is DNS propagation in action. In this complete guide, we explain everything: what DNS propagation is, why it takes time, how long it takes worldwide, and the fastest ways to check and troubleshoot it.
What is DNS Propagation?
DNS propagation is the process by which updates to your domain’s DNS records spread across all DNS servers worldwide after you make a change. When you update your DNS settings, such as changing your nameservers, modifying an A record, or updating your MX records, those changes do not appear instantly for everyone on the internet. Instead, they travel gradually from server to server across the global DNS network. This global DNS propagation time can range from a few minutes to 72 hours.
Think of the internet as a massive phone book system. Your domain name (like example.com) is the name in the book, and the DNS record is the phone number. When you “change your number,” every phone operator (DNS server) around the world needs to update their local copy of the book. Until they do, some people will still be calling the old number.
DNS Propagation Flow
| Your Domain (DNS Updated) |
→ | Root DNS Server |
→ | TLD Server (.com/.net) |
→ | ISP Resolver (Cache) |
→ | End User (Sees New IP) |
How DNS Works (and Why Propagation Happens)
To understand DNS propagation, you first need to understand how the Domain Name System works. DNS translates human-readable domain names into machine-readable IP addresses that servers use to communicate. Here’s the step-by-step DNS lookup process:
- Step 1 – Browser checks its local cache: Your browser stores recently visited DNS records. If it has the record cached (and it hasn’t expired), it uses that directly without any external request.
- Step 2 – OS checks its DNS cache: If the browser has no cached entry, it asks your operating system, which maintains its own DNS cache.
- Step 3 – Query sent to ISP’s recursive resolver: Your Internet Service Provider operates DNS resolver servers. These receive your DNS query and check their cache. This is where most propagation delays occur. ISP resolvers cache records aggressively.
- Step 4 – Resolver contacts root and authoritative servers: If the resolver doesn’t have a cached answer, it queries the root DNS servers, then TLD servers, then the authoritative nameserver for your domain, which has the latest record.
- Step 5 – Answer is cached and returned: The resolver stores the answer based on the TTL value and sends it back to your browser. The next request within the TTL window is answered from cache, which is why DNS propagation takes time.
How Long Does DNS Propagation Take?
How long does DNS propagation take? It varies, but here’s a practical breakdown of global DNS propagation time:
| Scenario | Typical Propagation Time | Speed |
| Low TTL records (300s / 5 min) | 5 – 30 minutes | Fast |
| Standard TTL records (3600s) | 1 – 4 hours | Moderate |
| A record / CNAME changes | 1 – 24 hours | Variable |
| MX record (email) changes | 4 – 24 hours | Variable |
| Nameserver changes | 12 – 48 hours | Slow |
| Domain transfer | 24 – 72 hours | Slowest |
| Full global propagation | Up to 72 hours | Maximum |
Key Factors That Affect DNS Propagation Time
TTL (Time to Live) Value
The TTL is the most important factor in DNS propagation time. It tells resolvers how long they should cache a record before checking for a fresh copy. A TTL of 86400 means 24 hours; a TTL of 300 means 5 minutes. If your TTL was 24 hours before your change, resolvers will serve the old record for up to 24 hours after your update.
ISP DNS Cache Behavior
Different ISPs refresh their DNS caches at different rates. Some respect the TTL exactly; others refresh less frequently. This means users on different ISPs may see your new DNS records at different times, creating inconsistent propagation across the globe.
Type of DNS Record Changed
Not all DNS records propagate at the same speed. A and CNAME changes propagate faster, while MX and nameserver updates take longer because they involve more layers of the DNS hierarchy.
Domain Registrar and Hosting Provider
Some registrars push nameserver updates to root servers faster than others. DNS hosting providers like Cloudflare or AWS Route 53 have infrastructure optimized for faster propagation.
Geographic Location
DNS propagation speed varies by location. Major internet hubs in North America and Western Europe typically see changes faster, while some regions in Asia and Africa may experience longer delays.
How to Check DNS Propagation Status
Knowing how to check DNS propagation is essential after making any DNS change. The goal is to verify that your new DNS records are being returned by resolvers around the world, not just on your local network.
Method 1: Use an Online DNS Propagation Checker
The easiest method is to use a dedicated DNS propagation checker tool that queries multiple DNS servers from locations worldwide and shows you the current record values from each. HasheTools offers a free online DNS propagation checker at hashetools.com that checks your domain against dozens of global resolvers simultaneously.
Method 2: Use Command Line Tools
For developers and sysadmins, command-line tools offer precise DNS lookup results:
• Windows (nslookup): nslookup example.com 8.8.8.8
• Mac/Linux (dig): dig @8.8.8.8 example.com A
Query different resolvers (8.8.8.8 = Google, 1.1.1.1 = Cloudflare, 9.9.9.9 = Quad9) to check propagation across multiple providers.
Method 3: Use Multiple Devices and Networks
Try accessing your website from different devices, your phone on mobile data, a friend’s computer, or a VPN, to see if different networks are serving the new or old DNS records.
Method 4: Clear Your Local DNS Cache
Before checking anything, clear your local DNS cache so you’re not seeing an outdated cached result:
- Windows: ipconfig /flushdns
- Mac: sudo dscacheutil -flushcache; sudo killall -HUP mDNSResponder
- Linux: sudo systemd-resolve –flush-caches
- Chrome: Visit chrome://net-internals/#dns and click ‘Clear host cache.’
DNS Propagation Troubleshooting
If your DNS changes are not reflecting, here are the most common causes and solutions:
| Problem | Likely Cause | Fix |
| The website shows old content | Local DNS or browser cache | Flush DNS cache; clear browser cache |
| Some users see new, others don’t | Propagation is still in progress | Wait for the full TTL to expire |
| DNS is correct, but the site won’t load | Firewall, SSL, or server config | Check server logs and SSL certificate |
| Email not working after MX change | MX propagation is still in progress | Wait 24 hrs; verify MX with dig |
| Nameserver change not taking effect | Registrar delay or wrong NS records | Confirm NS at registrar; wait 48 hrs |
| DNS propagated, but SSL error | SSL cert not yet on new host | Provision SSL cert on new server |
COMMON MISTAKE
Many users assume that because their DNS change is correct in the registrar panel, it has already propagated. This is wrong. The registrar is only the authoritative source; all caching resolvers in between need to expire their old cache before picking up the new record. Always check propagation with an external tool like HasheTools DNS Checker.
How to Speed Up DNS Propagation
While you cannot force instant global propagation, these proven strategies minimize DNS propagation delay and help your changes go live as quickly as possible:
- Lower your TTL before making changes: 48 hours before your planned DNS change, reduce your TTL to 300 seconds (5 minutes). Resolvers worldwide will cache the old record for only 5 minutes, drastically reducing propagation wait time when you make the actual change.
- Use a premium DNS provider with global anycast: Providers like Cloudflare, AWS Route 53, and Google Cloud DNS use anycast networks with nodes in hundreds of cities. Their DNS infrastructure propagates changes much faster than traditional shared hosting DNS.
- Clear your local DNS cache immediately: Flush the DNS cache on your machine and browser right after making changes. This lets you verify the new records are live without waiting for your local cache to expire.
- Switch to Google or Cloudflare DNS resolvers: Change your network’s DNS servers to 8.8.8.8 (Google) or 1.1.1.1 (Cloudflare). These resolvers typically refresh their caches faster than ISP resolvers.
- Plan migrations during low-traffic periods: Schedule DNS changes during off-peak hours (nights or weekends) so fewer users are affected during the transition period when some see the old site and others see the new one.
DNS Record Types and Their Propagation Times
Different DNS records (A, CNAME, MX, and others) have different propagation characteristics. Understanding these helps you set realistic expectations for each type of change:
| Record Type | Purpose | Typical Propagation | Impact |
| A Record | Maps the domain to an IPv4 address | 1 – 24 hours | Website accessibility |
| AAAA Record | Maps the domain to an IPv6 address | 1 – 24 hours | IPv6 accessibility |
| CNAME | Alias from one domain to another | 1 – 8 hours | Subdomains, CDN pointing |
| MX Record | Email server routing | 4 – 24 hours | Email delivery |
| TXT Record | SPF, DKIM, domain verification | 1 – 12 hours | Email authentication |
| NS Record | Defines authoritative nameservers | 12 – 48 hours | Entire DNS authority |
| SOA Record | Zone authority information | 24 – 72 hours | Zone administration |
| PTR Record | Reverse DNS lookup | 24 – 48 hours | Email reputation, security |
Frequently Asked Questions
What is DNS propagation and why does it happen?
DNS propagation is the time it takes for updated DNS records to spread across the Internet. It happens because DNS servers cache old records and only update them after the TTL (time to live) expires.
How long does DNS propagation take?
DNS propagation usually takes 24–72 hours worldwide, but many users see updates within a few hours. Timing depends on TTL, ISP caching, and location.
How can I check DNS propagation?
You can use tools like HasheTools DNS Checker or commands like nslookup and dig to see how your domain resolves in different locations.
Can DNS propagation be instant?
No, it cannot be fully instant worldwide. However, lowering your TTL before making changes can make updates much faster.
Why is my website not updating after DNS changes?
Your ISP or browser may still be using cached DNS data. Try clearing your cache, switching networks, or waiting for propagation to complete.
Does DNS propagation affect email?
Yes. Changes to MX records can temporarily affect email delivery. Keep your old mail server active for 48-72 hours to avoid issues.
Does clearing the DNS cache speed up propagation?
No, it only updates DNS on your device. It does not affect global propagation.
How can I verify DNS changes are correct?
Check your domain’s authoritative nameserver using tools like dig. If it shows the updated record, the change is correct and propagating.
Conclusion
DNS propagation is one of those technical realities of the internet that affects everyone who manages a website, email system, or online service. It’s not a bug or a failure; it’s simply how the distributed, cached DNS system keeps billions of lookups fast and efficient worldwide.

MTA-STS & TLS-RPT: How to Enforce Email Encryption & Monitor TLS Failures
Email remains one of the most critical communication channels for businesses, and one of the most targeted by attackers. While SPF, DKIM, and DMARC protect email identity, they do not secure email while it travels between mail servers.
This is where MTA-STS (Mail Transfer Agent Strict Transport Security) and TLS-RPT (TLS Reporting) become essential. Together, they enforce encryption in transit and give you full visibility into SMTP delivery failures, making them indispensable for any business that takes email security seriously.
Modern businesses also rely on tools like HasheTools to simplify email authentication, DNS validation, and security monitoring. With the right setup and proper visibility into your email infrastructure, you can prevent misconfigurations and ensure your emails are always delivered securely.
What is MTA-STS?
MTA-STS (Mail Transfer Agent Strict Transport Security) is an email security standard that forces SMTP connections between mail servers to use TLS encryption. It prevents attackers from intercepting messages or forcing a downgrade to an unencrypted connection.
Without MTA-STS: The Risks
- Emails may silently fall back to unencrypted SMTP
- Attackers can perform SMTP downgrade attacks to strip encryption
- Sensitive business data is exposed during transit
- No mechanism to reject insecure delivery attempts
With MTA-STS: The Benefits
- All inbound emails must arrive over TLS-encrypted connections
- Insecure connections are rejected, not just logged
- Man-in-the-middle attacks are blocked at the protocol level
- Works seamlessly alongside SPF, DKIM, and DMARC
What is TLS-RPT?
TLS-RPT (TLS Reporting) is a complementary protocol that automatically delivers failure reports to your inbox whenever a TLS-encrypted connection cannot be established. Think of it as the monitoring dashboard for MTA-STS.
Without TLS-RPT
- TLS failures happen silently; you have no visibility
- Email delivery problems are nearly impossible to debug
- Misconfigurations can go undetected for weeks
With TLS-RPT
- You receive structured JSON reports detailing every TLS failure
- Identify misconfigured mail servers before they cause delivery issues
- Monitor SMTP security posture in real time
- Supports compliance auditing and security documentation
MTA-STS vs. TLS-RPT: Key Differences
Although they work together, they serve fundamentally different purposes:
| Feature | MTA-STS | TLS-RPT |
|---|---|---|
| Purpose | Enforce TLS encryption | Report TLS failures |
| Function | Security enforcement | Monitoring & reporting |
| Action Taken | Blocks insecure email | Sends structured reports |
| Visibility | Silent enforcement | Detailed failure logs |
| Required? | Recommended | Strongly recommended |
Together, they form a complete email transport security system, one enforces, the other reports.
How MTA-STS Works: Step by Step
Step 1: Publish Your MTA-STS Policy File
Host a plain-text policy file at the following URL on your domain:
https://mta-sts.yourdomain.com/.well-known/mta-sts.txt
Example policy file content:
version: STSv1
mode: enforce
mx: mail.yourdomain.com
max_age: 86400
Step 2: Add the MTA-STS DNS TXT Record
Create a DNS TXT record to signal that MTA-STS is active on your domain:
_mta-sts.yourdomain.com TXT “v=STSv1; id=20260101”
The ID value must be updated whenever your policy file changes; it tells the sending servers that the policy has been refreshed.
Step 3: Send Mail Server Checks Your Policy
When another mail server attempts to deliver email to you, it automatically checks your DNS for the MTA-STS record, fetches the policy file from your subdomain, validates your mail server’s TLS certificate, and then proceeds only if everything matches.
Step 4: Secure Delivery or Rejection
- If TLS is valid and verified → email is delivered securely
- If TLS fails or the certificate is invalid → email is rejected (in enforce mode)
How TLS-RPT Works: Step by Step
Step 1: Add the TLS-RPT DNS Record
_smtp._tls.yourdomain.com TXT “v=TLSRPTv1; rua=mailto:reports@yourdomain.com”
Replace reports@yourdomain.com with any mailbox you monitor regularly. You can also send reports to a dedicated analytics service.
Step 2: Mail Servers Generate Reports
Whenever a sending mail server encounters a TLS issue when delivering to your domain, it automatically sends a structured JSON report to your specified address. Reports are sent once per day, per sending domain.
Step 3: Analyze the Reports
Each report contains detailed data, including:
- Number of successful and failed TLS connections
- Certificate validation errors (expired, mismatched, untrusted)
- STARTTLS negotiation failures
- MTA-STS policy violations
- Details of the sending mail server
How to Configure MTA-STS & TLS-RPT: Full Setup Guide
Step 1: Create the MTA-STS Subdomain
Create a subdomain in your DNS and point it to a web server that can serve HTTPS content:
mta-sts.yourdomain.com → your web server (HTTPS required)
Step 2: Upload the Policy File
Create and upload mta-sts.txt to your web server at the exact path:
/.well-known/mta-sts.txt
Full example policy:
version: STSv1
mode: enforce
mx: mail.yourdomain.com
mx: mail2.yourdomain.com
max_age: 604800
Step 3: Add MTA-STS DNS Record
_mta-sts.yourdomain.com TXT “v=STSv1; id=20260108”
Step 4: Add TLS-RPT DNS Record
_smtp._tls.yourdomain.com TXT “v=TLSRPTv1; rua=mailto:reports@yourdomain.com”
Step 5: Validate Your Setup
Use free tools to verify your configuration before going live:
- MXToolbox: check DNS record propagation
- Google Admin Toolbox: test MTA-STS policy retrieval
- dmarcian TLS-RPT analyzer: validate TLS report parsing
- Wait 24–48 hours for DNS propagation globally
MTA-STS vs. STARTTLS: Why the Upgrade Matters
| Feature | STARTTLS | MTA-STS |
|---|---|---|
| Encryption Type | Opportunistic | Enforced |
| Downgrade Protection | None easily bypassed | Strong rejects insecure |
| Certificate Validation | Optional | Mandatory |
| Attack Resistance | Vulnerable to MITM | Protected |
| Delivery Monitoring | None | Full (with TLS-RPT) |
STARTTLS upgrades connections to TLS if available, but an attacker can silently strip it and force plaintext delivery. MTA-STS eliminates this vulnerability.
Common MTA-STS & TLS-RPT Issues and How to Fix Them
1. Certificate Mismatch
Your MX server’s TLS certificate must match the hostname listed in your MTA-STS policy. Mismatches will cause legitimate emails to be rejected in enforce mode.
| Fix: Ensure your SSL certificate covers the exact MX hostnames in your policy file. Use wildcard certs or SAN certificates if needed. |
2. Incorrect or Missing MX Records
If your policy file lists MX hostnames that don’t match your actual DNS MX records, senders will be unable to validate your configuration.
| Fix: Run nslookup -type=MX yourdomain.com and verify every host listed in your mta-sts.txt matches exactly. |
3. Policy File Not Accessible Over HTTPS
The mta-sts.txt file must be served over HTTPS (not HTTP) with a valid certificate. If it returns a 404 or an HTTP redirect, MTA-STS will not activate.
| Fix: Test by visiting https://mta-sts.yourdomain.com/.well-known/mta-sts.txt in a browser; you should see the plain-text policy. |
4. Forgetting to Update the Policy ID
If you update your policy file but forget to change the ID value in the DNS TXT record, mail servers will continue caching the old policy.
| Fix: Always increment the ID (e.g., use a date like 20260108) whenever you make any change to your policy file. |
Best Practices for Email Transport Security
- Always start with mode: testing, collect data before enforcing
- Move to mode: enforce only after verifying reports show no legitimate failures
- Use valid, non-expired SSL/TLS certificates on all MX servers
- Monitor TLS-RPT reports weekly, set calendar reminders
- Update the policy ID value every time you modify the policy file
- Combine MTA-STS with SPF, DKIM, and DMARC for full email security coverage
- Keep MX server software updated to support modern TLS versions (1.2 minimum, 1.3 preferred)
- Audit DNS records quarterly to catch drift and misconfigurations early
Real-World Use Case: Financial Services Company
Consider a financial company sending invoices, contracts, and sensitive client data via email every day.
| Scenario | Without MTA-STS + TLS-RPT | With MTA-STS + TLS-RPT |
|---|---|---|
| Email Security | Vulnerable to interception | Fully encrypted in transit |
| Attack Exposure | MITM attacks possible | Downgrade attacks blocked |
| Issue Visibility | Problems invisible | Failures reported instantly |
| Compliance Risk | High audit failures are likely | Low documented & auditable |
| Client Trust | No verifiable assurance | Provable encryption standard |
For regulated industries, financial services, healthcare, legal, and government, MTA-STS and TLS-RPT are not optional enhancements. They are baseline security requirements.
Frequently Asked Questions (FAQ)
Does MTA-STS replace DMARC, SPF, or DKIM?
No. MTA-STS operates at a different layer. SPF, DKIM, and DMARC verify email identity and prevent spoofing. MTA-STS ensures the transport channel itself is encrypted. You need all of them for comprehensive protection.
How long does it take for MTA-STS to take effect?
DNS propagation typically takes 24–48 hours globally. However, sending mail servers also cache your policy for the duration of max_age (in seconds) specified in your policy file. Use a lower max_age during testing.
Will MTA-STS cause legitimate emails to be blocked?
Only if your TLS configuration is incorrect. This is why starting with mode: testing is critical; it lets you identify any misconfigurations before switching to enforce mode, where non-TLS connections are actively rejected.
Can I use TLS-RPT without MTA-STS?
Yes. TLS-RPT works independently and will report TLS failures even if MTA-STS is not implemented. However, the two protocols are designed to work together and provide maximum value when used in combination.
What format are TLS-RPT reports delivered in?
Reports are delivered as JSON files, often compressed as .gz attachments. You can parse them manually, use a spreadsheet, or use dedicated tools like DMARCian or Valimail to visualize the data.
Does MTA-STS affect outbound email?
MTA-STS only governs how other mail servers deliver email to your domain (inbound). However, if you send an email to domains that have MTA-STS enabled, your outgoing mail server must support TLS, or delivery will fail.
Conclusion
MTA-STS and TLS-RPT represent a major step forward in modern email security. While traditional protocols like STARTTLS rely on opportunistic encryption, they still leave room for downgrade attacks, misconfigurations, and a lack of visibility. MTA-STS solves the enforcement problem by ensuring that all inbound email connections are securely encrypted, while TLS-RPT provides the monitoring layer needed to detect and analyze any TLS-related delivery issues.
Together, these protocols create a strong, transparent, and enforceable email transport security system that works alongside SPF, DKIM, and DMARC to protect both identity and data in transit. For businesses that depend on email for sensitive communication, such as contracts, invoices, and client data, this is no longer optional; it is a required security standard in 2026.
Implementing and managing these configurations can be complex, especially when dealing with DNS records, policy files, and TLS validation. This is where HasheTools helps simplify the process by providing essential tools for DNS checks, email authentication validation, and security troubleshooting in one place. It allows businesses to quickly identify issues, validate configurations, and maintain a strong email security posture without unnecessary complexity.

DNSSEC Explained: Why Most Domains Are Still Vulnerable in 2026
DNS is one of the most critical systems on the internet, yet it remains one of the least protected. Every time someone visits your website, sends you an email, or connects to your services, they rely on DNS to get the correct destination. The problem? Traditional DNS offers no built-in way to verify whether the response it returns is legitimate or forged.
This is exactly the gap DNSSEC (Domain Name System Security Extensions) was designed to fill. By adding cryptographic signatures to DNS records, DNSSEC allows resolvers to verify that the data they receive is authentic and hasn’t been tampered with. It transforms DNS from a trust-based system into a verifiable one.
And yet, despite being available for over 20 years, most domains in 2026 are still vulnerable. In this guide, we’ll break down how DNSSEC works, why adoption remains low, and what risks you face if your domain isn’t protected.
What is DNSSEC?
DNSSEC stands for Domain Name System Security Extensions. It is an additive security layer for DNS that uses public-key cryptography to sign DNS records, allowing resolvers to verify that the records they receive are authentic and unaltered.
The core problem DNSSEC solves: DNS was designed to be fast and lightweight, not secure. A standard DNS response carries no proof of authenticity; a resolver receiving an answer has no built-in way to tell whether it came from the legitimate authoritative nameserver or from an attacker who injected a forged response. DNSSEC fixes this by turning DNS records into signed, verifiable data.
DNSSEC does NOT encrypt DNS traffic (that’s DNS-over-HTTPS or DNS-over-TLS). What it does instead is provide data integrity and origin authentication; you can verify what the answer says and who it came from, even though the data travels in plaintext.
The Analogy: DNSSEC as a Wax Seal: Imagine sending a letter through the postal system in medieval times. Anyone handling the letter could open it and replace its contents. Adding a wax seal doesn’t stop anyone from reading the letter, but it does let the recipient verify that the seal is unbroken, confirming the letter hasn’t been tampered with and truly came from the claimed sender. DNSSEC’s cryptographic signatures work on the same principle: they don’t hide the DNS data, but they make tampering detectable.
The DNS Vulnerability DNSSEC Solves
To understand why DNSSEC matters, you first need to understand how DNS can be attacked without it.
The Kaminsky Attack: DNS’s Worst Nightmare
In 2008, security researcher Dan Kaminsky revealed a fundamental vulnerability in DNS that sent shockwaves through the industry. His technique, now called the Kaminsky Attack, could poison a recursive resolver’s cache in seconds using a simple but devastating exploit.
How the Kaminsky Attack Works
- Attacker targets: Picks the victim’s resolver and a target domain
- Floods with queries: Queries for random.target.com subdomains
- Sends fake replies: Races to answer with forged DNS response
- Guesses txn ID: 16-bit space = 65,536 possibilities
- Poisons the cache: Fake record cached for full TTL duration
Why was it so dangerous? DNS transaction IDs are only 16 bits, meaning there are only 65,536 possible values. By querying for non-existent subdomains (which the resolver had to look up fresh each time) and flooding with forged responses, an attacker could statistically expect to guess the right transaction ID within seconds. Once poisoned, the forged record would be served to every user of that resolver for the duration of its TTL, potentially for hours or days.
The emergency patch, randomising source ports to add another ~16 bits of randomness, bought time but didn’t fundamentally solve the problem. DNSSEC is the definitive fix.
What an Unprotected DNS Response Looks Like
| Standard DNS response, no authentication, no verification |
| $ dig hashetools.com A
;; ANSWER SECTION: hashetools.com. 300 IN A 104.21.45.67 # This response contains: # ✓ The IP address (104.21.45.67) # ✗ No signature, could be from a legitimate server OR an attacker # ✗ No proof that the data hasn’t been modified in transit # ✗ No chain of trust back to any verified root # A forged response looks identical. The resolver cannot tell the difference. |
Who Is Actively Exploiting Unprotected DNS in 2026? Nation-state actors (documented campaigns from Iran, Russia, China, and North Korea targeting government and critical infrastructure domains), ransomware operators using DNS hijacking for initial access and C2 communication, phishing campaigns using lookalike domains that exploit unprotected resolvers, and malware using DNS cache poisoning to redirect software update servers to deliver malicious payloads. If your domain lacks DNSSEC, any of these actors can forge records for your domain against unvalidating resolvers.
How DNSSEC Works: Cryptographic Signatures Explained
DNSSEC adds digital signatures to DNS records using asymmetric public-key cryptography, the same mathematical foundation used in HTTPS certificates and code signing.
The Basic Mechanism
- The zone owner (your DNS provider or authoritative server) generates a key pair: a private signing key and a public verification key
- Every DNS record set (all A records for your domain, all MX records, etc.) is signed using the private key, producing a digital signature stored in an RRSIG record
- The public key is published in the DNS zone itself, in a DNSKEY record, so anyone can retrieve and use it to verify signatures
- When a resolver receives a DNS response, it retrieves the DNSKEY and verifies the RRSIG signature. If the signature is valid, the data is authentic; if the signature is invalid or missing, the response is rejected
- The public key itself is verified by a digital signature from the parent zone, creating a chain of trust all the way back to the signed DNS root
What a DNSSEC-Protected Response Looks Like
| DNSSEC-enabled DNS response, with cryptographic proof |
| $ dig hashetools.com A +dnssec
;; ANSWER SECTION: hashetools.com. 300 IN A 104.21.45.67 hashetools.com. 300 IN RRSIG A 13 2 300 20261231000000 ( 20261201000000 12345 hashetools.com. Xy9zABCDEFGH1234… ) # Digital signature ;; ADDITIONAL SECTION: hashetools.com. 3600 IN DNSKEY 257 3 13 ( mdsswUyr3DPW132mOi8V9xESWE8jTo0d… ) # Zone’s public key # This response contains: # ✓ The IP address (104.21.45.67) # ✓ RRSIG: cryptographic signature over the A record # ✓ DNSKEY: public key to verify the signature # ✓ Chain of trust verified back to the DNS root # ✓ Any tampering invalidates the signature, immediately detectable |
The Two Key Types in DNSSEC
DNSSEC uses two types of keys in a two-layer signing architecture:
| Key Type | Abbreviation | What It Signs / Purpose |
|---|---|---|
| Key Signing Key | KSK | Signs the ZSK DNSKEY record. Longer-lived. Its hash (DS record) is stored in the parent zone to create the chain of trust. |
| Zone Signing Key | ZSK | Signs all the actual DNS records in the zone (A, MX, TXT, CNAME, etc.). Rotated more frequently than the KSK. |
Why two keys? Separating the roles allows the ZSK (which signs many records and must be used frequently) to be rotated often without changing the KSK (which is anchored in the parent zone via a DS record and is more complex to rotate). This is analogous to having a master key and working keys; the working key can be changed without replacing the master.
The DNSSEC Record Types You Need to Know
DNSSEC introduces four new DNS record types that work together to provide authentication. Understanding them is essential for troubleshooting and configuration.
| Record Type | Full Name | What It Contains / Does |
|---|---|---|
| DNSKEY | DNS Public Key | Stores the zone’s public keys (ZSK and KSK). Published in the DNS zone itself. Resolvers use this to verify RRSIG signatures. |
| RRSIG | Resource Record Signature | The digital signature over a set of DNS records (called an RRset). One RRSIG per record type per zone. Signed with the ZSK. |
| DS | Delegation Signer | A hash of the child zone’s KSK DNSKEY. Published in the PARENT zone. Creates the link between parent and child in the chain of trust. |
| NSEC / NSEC3 | Next Secure / Next Secure v3 | Proves that a domain or record type does NOT exist. Prevents attackers from returning forged NXDomain responses. NSEC3 hashes the names for privacy. |
DNSKEY Record Anatomy
| DNSKEY record: your zone’s public key |
| Flags: 257 # 257 = KSK (Zone Signing Key + SEP flag), 256 = ZSK |
| Protocol: 3 # Always 3 for DNSSEC |
| Algorithm: 13 # 13 = ECDSA P-256 with SHA-256 (recommended in 2026) |
| PublicKey: mdsswUyr3… # Base64-encoded public key, used to verify RRSIG signatures |
RRSIG Record Anatomy
| RRSIG records the digital signature over your DNS records |
| TypeCovered: A # Record type this signature covers |
| Algorithm: 13 # Must match the DNSKEY algorithm |
| Labels: 2 # Number of domain labels in the name |
| TTL: 300 # Original TTL of the signed records |
| Expiration: 20261231000000 # Signature validity end (YYYYMMDDHHMMSS) |
| Inception: 20261201000000 # Signature validity start |
| KeyTag: 12345 # Identifies which DNSKEY was used to sign |
| Signature: Xy9zABCD… # The base64-encoded digital signature |
DS Record Anatomy
| DS record: published in the PARENT zone (your registrar / TLD) |
| KeyTag: 12345 # Matches the KeyTag in the child’s KSK DNSKEY |
| Algorithm: 13 # Hash algorithm (13 = ECDSA) |
| DigestType: 2 # 2 = SHA-256 (recommended) |
| Digest: AB12CD34… # SHA-256 hash of the child zone’s KSK DNSKEY |
The Chain of Trust: From Root to Your Domain
DNSSEC’s power comes from a hierarchical chain of trust that extends from a single globally trusted root, the DNS Root Zone, all the way down to your individual domain records. Every link in this chain is cryptographically verified.
| DNS Root Zone ( . )
Trust Anchor, maintained by ICANN, signed by the Root KSK (rotated by ICANN, last major rotation 2018, upgraded 2026) |
| │ Root KSK signs Root ZSK │ Root ZSK signs .com DS record |
| TLD Zone ( .com / .org / .net / etc. )
Operated by Verisign (.com), PIR (.org), etc. Contains DS records for registered domains. |
| │ TLD nameserver publishes DS record → links to your domain’s KSK |
| Your Domain ( yourdomain.com )
Your DNS zone contains DNSKEY records (KSK + ZSK) and RRSIG signatures over every record set. |
| │ ZSK signs every DNS record in your zone (A, MX, TXT, CNAME, NS, SOA…) |
| Individual DNS Records (A, MX, TXT, CNAME…)
Each record set has a corresponding RRSIG. Resolver validates RRSIG → DNSKEY → DS → TLD → Root. Chain complete. |
Breaking the chain: If any link in this chain is missing or invalid, if your registrar didn’t submit your DS record to the TLD, if your RRSIG has expired, if the algorithm in your DNSKEY doesn’t match your RRSIG, the entire DNSSEC validation fails. DNSSEC-validating resolvers will refuse to serve the response, resulting in SERVFAIL errors for your users.
Why Most Domains Still Don’t Have DNSSEC in 2026
DNSSEC was standardised in RFC 4033–4035 in 2005. In 2026, two decades later, fewer than 25% of registered domains have it enabled. This is one of the most persistent adoption failures in cybersecurity. Here’s why:
Operational Complexity
DNSSEC requires managing key pairs, signing zones, submitting DS records to registrars, coordinating key rollovers, and monitoring signature expiry. For organisations without dedicated DNS expertise, this is daunting.
Signature Expiry Risk
RRSIG records have an expiration date, typically 30 days. If signatures aren’t refreshed before expiry (automatically by the DNS provider or manually), the domain goes into SERVFAIL for all validating resolvers. This ‘break everything’ failure mode makes operations teams reluctant to enable it.
Key Rollover Complexity
Rotating DNSSEC keys safely requires a precise multi-step dance between the child zone and the parent (registrar). A mistimed rollover breaks the chain of trust. Automated key management has improved but remains error-prone in many environments.
Registrar / Provider Support Gaps
Not all DNS providers and registrars support DNSSEC, or support it well. Many budget hosting providers, legacy DNS platforms, and smaller registrars offer no DNSSEC support at all, leaving their customers unable to enable it regardless of intent.
Invisible Protection
DNSSEC protects against attacks that most domain owners have never personally experienced. The risk is real but invisible; unlike an SSL error (which shows a red browser warning), a DNS cache poisoning attack is completely invisible to the victim. Low perceived urgency → low adoption.
No Direct Business Incentive
SSL certificates have a visible browser padlock that drives adoption through customer-facing consequences. DNSSEC has no equivalent visible signal. There is no ranking boost, no browser warning for its absence, and no direct customer-facing benefit that organisations can point to when justifying the operational cost.
Global Coordination Required
DNSSEC requires both the domain owner, the registrar, and the TLD operator to support and correctly configure it. A failure at any party breaks the chain. Coordinating across these three separate entities, especially for legacy domains, creates inertia.
2026 Adoption Trends: A Reason for Optimism: While overall adoption remains low, the trajectory is improving. Cloud-managed DNS providers (Cloudflare, AWS Route 53, Google Cloud DNS) now enable DNSSEC with a single click and handle all key management automatically. The ccTLD adoption rate is much higher than that of commercial domains. .gov domains in the US are mandated to use DNSSEC. ICANN’s 2026 root zone upgrades are prompting renewed attention to DNSSEC at all levels of the hierarchy.
DNSSEC Advantages and Limitations
| Advantages of DNSSEC | Challenges & Limitations |
| Eliminates DNS cache poisoning attacks against your domain | Does NOT encrypt DNS traffic (use DoH/DoT for that) |
| Provides cryptographic proof of DNS record authenticity | Does NOT prevent DNS hijacking at the registrar level |
| Protects against Kaminsky-style forged response injection | Misconfiguration causes a complete domain outage (SERVFAIL) |
| Enables DANE, binding TLS certificates to DNS records | RRSIG signatures expire and require active maintenance |
| Enables SSHFP, verifying SSH host keys via DNS | Key rollovers require careful coordination with the registrar |
| Provides authenticated denial of existence (NSEC/NSEC3) | Increases DNS response size (adds RRSIG + DNSKEY records) |
| Required for some government and compliance frameworks | Not all DNS providers/registrars support it |
| Free to enable, no ongoing certificate cost | NSEC records can enable zone enumeration (use NSEC3) |
| Increasingly automated by major DNS providers | Amplification: larger responses can be abused in DDoS |
| Protects users even when they can’t see it working | Low validator adoption limits end-to-end protection |
How to Check if Your Domain Has DNSSEC
Before configuring DNSSEC, verify your current status. There are multiple ways to check:
Method 1: HasheTools DNS Lookup
The quickest method for most users: go to hashetools.com, open the DNS Lookup tool, enter your domain, and look for DNSKEY and RRSIG records in the results. If they appear, DNSSEC is enabled. If they don’t, it is not.
Method 2: Command Line (dig)
| Check for DNSSEC records using dig |
| # Check for DNSKEY record (your zone’s public key)
dig yourdomain.com DNSKEY +short # If DNSSEC is enabled, you’ll see output like: # 257 3 13 mdsswUyr3DPW132mOi8V9xESWE8jTo0d… (KSK) # 256 3 13 oJMRESz5E4gYzS/q6XDrvU1/6STjwd1D… (ZSK) # Check for RRSIG records (signatures over your A record) dig yourdomain.com A +dnssec +short # DNSSEC enabled: returns A record AND RRSIG record # DNSSEC not enabled: returns only A record, no RRSIG # Check DS record (published at your registrar / TLD) dig yourdomain.com DS +short # If no DS record: chain of trust is broken, DNSSEC not propagated |
Method 3: DNSSEC Analyser Tools
| Full DNSSEC chain validation: online tools |
| # ICANN DNSSEC Analyser:
# https://dnssec-analyzer.verisignlabs.com/yourdomain.com # DNSViz, detailed visual chain of trust analysis: # https://dnsviz.net/d/yourdomain.com/dnssec/ # Cloudflare DNSSEC Debugger: # https://dnssec-debugger.verisignlabs.com/ # Look for: # Green checkmarks = valid chain of trust # Red X = broken link in chain # Yellow warning = configuration issue (often expiring signatures) |
Interpreting Your Results
| What You See | What It Means |
|---|---|
| DNSKEY + RRSIG records present, DS record in TLD | DNSSEC is fully enabled, and the chain of trust is intact. |
| DNSKEY + RRSIG records present, no DS record | DNSSEC is configured in the zone, but the DS record is not submitted to the registrar. Chain of trust broken, not validated. |
| No DNSKEY, no RRSIG records | DNSSEC is not enabled on your domain. All DNS responses are unauthenticated. |
| RRSIG records present but expired | Signatures have passed their validity date. Validating resolvers return SERVFAIL. The domain is effectively unreachable. |
| SERVFAIL when querying your domain | DNSSEC is configured but broken, expired signatures, missing DS record, algorithm mismatch, or failed key rollover. Urgent fix required. |
How to Enable DNSSEC: Step-by-Step Guide
The exact steps vary by DNS provider and registrar, but the fundamental process is the same for everyone. Here is the complete workflow:
Before You Start: Confirm that both your DNS provider (who hosts your DNS zone) and your domain registrar (where you registered the domain) support DNSSEC. They may be the same company (e.g., if you use Cloudflare for both) or different companies (e.g., GoDaddy as registrar, AWS Route 53 as DNS provider). If your DNS provider doesn’t support DNSSEC, you’ll need to migrate your DNS before enabling it.
Step 1: Enable DNSSEC Signing in Your DNS Provider
- Log in to your DNS provider’s dashboard
- Navigate to the DNS settings for your domain
- Find the DNSSEC option (usually labelled ‘DNSSEC’, ‘DNS Security’, or ‘DNSSEC Signing’)
- Enable DNSSEC signing, the provider will generate a KSK and ZSK, and begin signing your zone.
- The provider will display a DS record (containing the KeyTag, Algorithm, DigestType, and Digest). Copy this exactly; you’ll need it in Step 2
Step 2: Submit the DS Record to Your Registrar
- Log in to your domain registrar (where you purchased the domain)
- Navigate to the DNS or DNSSEC settings for your domain
- Find the ‘Add DS Record’ or ‘DNSSEC’ section
- Enter the DS record values provided by your DNS provider: Key Tag, Algorithm, Digest Type, Digest.
- Save the DS record; the registrar will publish it in the TLD zone
- Wait for propagation, DS records typically propagate within 1–48 hours
Step 3: Verify the Chain of Trust
| Verify your complete DNSSEC chain after configuration |
| # Step 1: Confirm DNSKEY is published
dig yourdomain.com DNSKEY +short # Should return 2 records: one KSK (flags=257), one ZSK (flags=256) # Step 2: Confirm DS record is in the TLD zone dig yourdomain.com DS +short # Should return your DS record, matches the KSK hash # Step 3: Confirm RRSIG is present on your A record dig yourdomain.com A +dnssec # Should return: A record + RRSIG record # Step 4: Full chain validation dig yourdomain.com A +sigchase +trusted-key=/etc/trusted-key.key # Or use DNSViz online for a visual chain check |
Step 4: Set Up Monitoring
- Monitor RRSIG expiry: RRSIG records have an expiration date. Your DNS provider should auto-renew them, but set up an alert in case auto-renewal fails.
- Monitor DS record consistency: Periodically verify that the DS record at your registrar matches your current KSK.
- Set up DNSSEC failure alerts: Tools like Zabbix, Nagios, or cloud monitoring services can alert you if your domain starts returning SERVFAIL.
- Use HasheTools DNS Lookup regularly: Quick periodic checks confirm DNSKEY and RRSIG records remain present and valid.
Key Rollover: The Critical Ongoing Operation: ZSK rotation should happen every 30–90 days. KSK rotation is less frequent (annually or as needed) but more complex; it requires updating the DS record at your registrar. Most managed DNS providers handle ZSK rotation automatically. KSK rotation typically requires manual action: generate new KSK → publish both old and new DNSKEY simultaneously (pre-publication) → update DS record at registrar → remove old DNSKEY after DS has propagated. Never remove the old DNSKEY before the new DS record has propagated globally.
DNSSEC by DNS Provider: Quick Reference
DNSSEC support and ease of configuration vary significantly by provider. This table covers the most commonly used DNS providers and registrars as of 2026:
| Provider | DNSSEC Support | Auto Key Mgmt | How to Enable |
|---|---|---|---|
| Cloudflare | Full | Automatic | DNS → DNSSEC tab → Enable DNSSEC. The DS record is displayed automatically. |
| AWS Route 53 | Full | Automatic | Hosted Zone → Enable DNSSEC Signing → Register DS with registrar. |
| Google Cloud DNS | Full | Automatic | Cloud DNS → Zone → DNSSEC → Enable. DS record provided. |
| Cloudflare Registrar | Full | Automatic | One-click if DNS is also on Cloudflare, DS is submitted automatically. |
| GoDaddy DNS | Partial | Manual keys | Domain Settings → DNS → DNSSEC. Must manage key rotation manually. |
| Namecheap | Partial | Limited | Advanced DNS → DNSSEC. Key management support varies by plan. |
| Name.com | Supported | Manual | Manage Domain → DNS Records → DNSSEC Records. |
| Porkbun | Supported | Auto if Porkbun DNS | Domain → Edit → DNSSEC. Auto if using Porkbun DNS. |
| cPanel / WHM | Depends | Provider-dependent | Depends on the hosting provider’s DNS server configuration. |
| Generic BIND | Full (manual) | Manual only | Use dnssec-keygen + dnssec-signzone. Requires significant expertise. |
| PowerDNS | Full | Auto-signing | pdnsutil secure-zone yourdomain.com, then submit the DS record. |
Recommendation: Use a Provider That Automates DNSSEC: The biggest cause of DNSSEC-related outages is expired RRSIG signatures that weren’t refreshed in time. Choosing a DNS provider that handles key generation, zone signing, and signature renewal automatically (Cloudflare, AWS Route 53, Google Cloud DNS) eliminates the most dangerous operational risks. If your current provider doesn’t support automatic DNSSEC management, consider migrating your DNS before enabling DNSSEC.
DNSSEC and Email Security: The Connection
DNSSEC has a direct and important relationship with email security, specifically through DANE (DNS-based Authentication of Named Entities), an extension that allows you to publish your mail server’s TLS certificate fingerprint in DNS and have it validated via DNSSEC.
What is DANE?
DANE (RFC 7671) allows you to publish a TLSA record in DNS that specifies which TLS certificate or Certificate Authority your mail server uses. Receiving mail servers that support DANE can verify this record, and reject connections if the certificate doesn’t match, even if the presented certificate is ‘valid’ according to traditional CA verification.
This closes a significant gap in email security: traditional STARTTLS encryption for email is opportunistic and can be stripped by a man-in-the-middle attacker. DANE makes TLS enforcement mandatory and verifiable.
| DANE TLSA record for email: published in DNSSEC-signed zone |
| # TLSA record for your mail server (MX record host)
# Format: _port._protocol.hostname TLSA usage selector matchingtype hash _25._tcp.mail.yourdomain.com. IN TLSA 3 1 1 ( AB12CD34EF56… ) # Usage 3 1 1 = DANE-EE: Domain-issued cert, SubjectPublicKeyInfo, SHA-256 # Requires: DNSSEC enabled on yourdomain.com + STARTTLS on your mail server |
DNSSEC + Email Authentication Stack
| Protocol | Role in Email Security |
|---|---|
| SPF | Authorises sending IPs for your domain (DNS TXT record, benefits from DNSSEC authentication) |
| DKIM | Cryptographically signs email messages (DNS TXT record, DNSSEC prevents forging of public key) |
| DMARC | Enforces SPF/DKIM policy and alignment (DNS TXT record, DNSSEC prevents policy tampering) |
| BIMI | Displays brand logo in inbox (DNS TXT record, DNSSEC prevents logo URL hijacking) |
| DANE / TLSA | Pins TLS certificate for SMTP, requires DNSSEC. Makes opportunistic TLS into verified TLS. |
| MTA-STS | Alternative to DANE for enforcing SMTP TLS, does not require DNSSEC, but is complementary |
The key insight: SPF, DKIM, DMARC, and BIMI records are all DNS TXT records. Without DNSSEC, an attacker with access to a poisoned resolver could forge any of these records, serving a modified SPF record that authorises their own servers, or a modified DKIM public key that lets them forge signed messages. DNSSEC protects the integrity of your entire email authentication infrastructure.
DNSSEC vs. DNS-over-HTTPS: Understanding the Difference
These two technologies are frequently confused because they both improve DNS security. They are complementary, not competing; they solve different problems at different layers.
| Attribute | DNSSEC | DNS-over-HTTPS (DoH) |
|---|---|---|
| What it protects | DNS data integrity and origin authenticity | DNS query privacy in transit |
| What it prevents | Cache poisoning, forged responses | Eavesdropping, on-path query manipulation |
| Encryption | No, data travels in plaintext | Yes, full encryption of DNS query and response |
| Authentication | Yes, cryptographic proof of record origin | No, doesn’t verify record authenticity |
| Where configured | DNS zone (server-side) + registrar | Client device or resolver |
| Failure mode | SERVFAIL (breaks resolution) | Falls back to standard DNS if DoH is unavailable |
| Protects against the ISP | No, ISP can still see (not forge) records | Yes, ISP cannot see or modify queries |
| Required by | DANE, SSHFP, some compliance frameworks | Privacy regulations, some enterprise policies |
| 2026 adoption | < 25% of domains | ~35% of DNS queries globally (Mozilla/Cloudflare) |
Use both: DNSSEC validates that the DNS records themselves are authentic. DoH ensures that nobody on the network path can observe or tamper with your DNS queries. Together, they provide comprehensive DNS security: authenticated data delivered over an encrypted channel.
The Complete DNS Security Stack for 2026: Enable DNSSEC on your domain (protects your DNS records from forgery) + Enable DoH/DoT on your resolver and endpoints (protects query privacy and on-path manipulation) + Enable DANE/TLSA for your mail servers (cryptographically binds your TLS certificates to DNSSEC) + Monitor continuously with HasheTools (catches misconfigurations and attacks early). This four-layer approach closes the major DNS attack surfaces described in this guide.
Frequently Asked Questions
What happens if DNSSEC is misconfigured?
Validating resolvers like Google (8.8.8.8), Cloudflare (1.1.1.1), and Quad9 will return SERVFAIL, making your website, email, and all DNS-dependent services completely unreachable. This is why monitoring RRSIG expiry and DS record consistency is critical after enabling DNSSEC.
Will DNSSEC slow down my DNS resolution?
Marginally. It adds a few milliseconds of cryptographic validation and slightly larger responses, but in practice, the impact is negligible. Responses are still cached normally, and the security benefit far outweighs the cost.
Do I need DNSSEC if I already use Cloudflare or a CDN?
Yes. CDNs protect at the application layer, but they can’t stop DNS cache poisoning at the resolver level. An attacker who poisons a resolver redirects users before they ever reach your CDN. DNSSEC stops the attack before that happens.
What algorithm should I use?
ECDSA P-256 with SHA-256 (Algorithm 13) is the 2026 recommendation, strong security, small keys, and fast validation. Ed25519 (Algorithm 15) is a great alternative. Avoid RSA-SHA1; SHA-1 is cryptographically deprecated.
How do I fix a broken DNSSEC chain?
Use DNSViz (dnsviz.net) to identify the broken link. Expired RRSIG, re-sign the zone. Missing DS record, resubmit it to your registrar. Missing DNSKEY, re-enable signing in your DNS provider. Then verify with HasheTools DNS Lookup and allow up to 48 hours for propagation.
Is DNSSEC required by regulations?
Yes, in several frameworks. US OMB mandates it for all .gov domains. The EU’s NIS2 Directive requires it for critical infrastructure operators. PCI-DSS v4.0 includes relevant DNS security controls. Many government procurement contracts now extend this requirement to vendor domains.
Conclusion
DNSSEC fixes a fundamental flaw in the Internet’s infrastructure, one that no amount of application-layer security can patch. Without it, your DNS records, including SPF, DKIM, and DMARC, can be silently forged against vulnerable resolvers.
The operational barrier is lower than ever. Major providers like Cloudflare, AWS Route 53, and Google Cloud DNS automate key management and signature renewal entirely. Enabling DNSSEC can take under five minutes.
In 2026, it shouldn’t be optional. Pair it with DoH/DoT for transport privacy, DANE for mail server certificate pinning, and continuous monitoring, because when DNS is compromised, everything built on top of it is at risk.

DNS Hijacking, Spoofing & Tunneling: How Attackers Exploit DNS in 2026
DNS hijacking, spoofing, and tunneling are cyberattack techniques that exploit the Domain Name System, the internet’s directory service, to redirect users to malicious sites, intercept traffic, or secretly exfiltrate data. Because virtually all network traffic relies on DNS, attackers who can manipulate DNS responses gain powerful control over what a user or system actually connects to.
Why DNS Is a Prime Target
DNS was designed in the 1980s for a small academic network. Security was never a priority. Most DNS traffic travels unencrypted over UDP port 53, making it observable, interceptable, and manipulable by anyone on the network path between your device and the DNS server.
What makes it especially dangerous:
- Unencrypted by default: DNS queries are transmitted in plaintext, visible to any observer
- Trust-based and stateless: resolvers accept the first matching response; they don’t verify the sender’s identity
- Cached responses: a poisoned cache entry persists for its full TTL, affecting every user on that resolver
- Rarely monitored: most organisations actively watch HTTP/HTTPS traffic but treat DNS as invisible infrastructure
DNS is exploited at every stage of a modern attack: reconnaissance, phishing, command-and-control, and data exfiltration, all hiding inside a protocol that firewalls seldom block.
DNS Hijacking: The Redirect Attack
DNS hijacking alters DNS resolution so that a domain resolves to an IP address controlled by an attacker. Unlike spoofing, hijacking involves persistent modifications to DNS infrastructure, making it harder to detect and longer-lasting.
Types of DNS Hijacking
| Type | How It Works |
| Router hijacking | An attacker compromises your router and changes its DNS server settings to a rogue resolver |
| Local hijacking | Malware modifies the local hosts file or DNS client settings on your device |
| Registrar hijacking | An attacker gains access to your registrar account and changes your authoritative nameservers |
| Authoritative NS hijack | Attacker compromises the nameserver itself; changes affect every resolver worldwide |
Real-World Example: DNSpionage
The DNSpionage campaign (2018–2019, attributed to Iranian threat actors) compromised domain registrar accounts for government and commercial targets across the Middle East, redirecting traffic through attacker-controlled servers and capturing credentials for months before detection. Nation-state actors continue to use registrar-level hijacking as a primary espionage technique in 2026.
Signs Your Domain May Be Hijacked
- DNS propagation checkers show different IPs across global resolvers
- Your registrar sends unexpected NS record change notifications
- SSL/TLS certificate monitoring fires unexpectedly for your domain
- Users report being redirected to login pages that look like yours
- Unexpected DMARC reports show unfamiliar sending sources
DNS Spoofing & Cache Poisoning
DNS cache poisoning injects a fraudulent DNS record into a recursive resolver’s cache. Once poisoned, the resolver serves the attacker’s forged answer to every client that queries for that domain, until the cache entry expires.
How It Works
DNS resolvers accept UDP responses that match the query’s transaction ID (a 16-bit number). If an attacker can guess or brute-force that ID and send a forged response before the legitimate nameserver replies, the resolver accepts and caches the fake answer.
In 2008, researcher Dan Kaminsky demonstrated a devastating variant that could poison a resolver in seconds, forcing emergency patching of nearly all DNS software worldwide. In 2026, modern variants combine Kaminsky-style flooding with IP fragmentation exploitation and side-channel timing attacks.
Hijacking vs. Spoofing: Key Differences
| Attribute | DNS Spoofing / Cache Poisoning | DNS Hijacking |
| Target | Recursive resolver cache | DNS infrastructure (registrar, NS, router) |
| Persistence | Temporary (until TTL expires) | Persistent until discovered |
| Requires system access? | No, network-level attack | Yes, account/system compromise |
| Affected users | All users of the poisoned resolver | All users of the domain globally |
| Primary defence | DNSSEC, DNS-over-HTTPS | Registrar lock, MFA, NS monitoring |
DNSSEC: The Technical Defence
DNSSEC cryptographically signs DNS records. A resolver that validates DNSSEC signatures can detect a forged response, even one with the correct transaction ID, because the signature won’t match. Despite being standardised in 2005, DNSSEC adoption remains below 30% globally, leaving the majority of DNS traffic vulnerable.
Check if your domain has DNSSEC enabled:
dig yourdomain.com DNSKEY +dnssec
# A valid response includes RRSIG records.
# If no RRSIG records appear, DNSSEC is not enabled.
DNS Tunneling: Hiding Data in Plain Sight
DNS tunneling encodes arbitrary data, commands, stolen files, malware payloads, inside DNS queries and responses. It exploits the fact that DNS traffic is almost universally permitted through firewalls, even in highly locked-down environments.
Firewalls block unusual outbound ports. But DNS on UDP port 53 is rarely blocked; doing so would break internet access entirely. Attackers build covert channels over a protocol that security teams rarely inspect.
What Gets Tunneled
- Command & control (C2): Malware receives attacker instructions via DNS TXT records, bypassing corporate firewalls entirely
- Data exfiltration: Sensitive files are base64-encoded and split across hundreds of DNS queries; the attacker’s nameserver reassembles them
- VPN bypass: Tools like iodine and dns2tcp create functional IP tunnels over DNS, enabling full internet access through captive portals
- Malware staging: Payloads are downloaded through DNS, bypassing HTTP/HTTPS filtering
What Tunneled Traffic Looks Like
# LEGITIMATE: Short subdomain, common record type
dig hashetools.com A
# hashetools.com. 300 IN A 104.21.45.67
# TUNNELED: Long encoded subdomain, TXT record
dig aGVsbG8gd29ybGQgdGhpcyBpcyBzdG9sZW4gZGF0YQ.evil.com TXT
# Red flags: long base64 subdomain + TXT query + unknown domain
DNS Tunneling Red Flags
| Indicator | Why It’s Suspicious |
| Subdomain length > 50 characters | Legitimate subdomains are short; long base64 labels indicate data encoding |
| High query rate to a single domain | Tunneling tools make rapid-fire queries abnormal for legitimate use |
| Unusual record types (TXT, NULL) | Tunneling tools favour TXT records to carry payload data |
| Unknown or newly registered domains | Attacker infrastructure is often freshly registered |
| Large DNS response sizes | TXT records carrying C2 commands are far larger than typical responses |
DNS Rebinding Attacks
DNS rebinding tricks a victim’s browser into treating an attacker-controlled server as if it were on the victim’s local network, bypassing the same-origin policy and exposing internal services.
How it works:
- Victim visits attacker’s domain (via phishing or malicious ad)
- Domain resolves to the attacker’s real server with a very short TTL (1 second)
- TTL expires; next DNS lookup returns a private IP (192.168.x.x or 10.x.x.x)
- The browser now treats the attacker’s domain as a local network address
- JavaScript can now read responses from routers, NAS devices, internal panels, and IoT devices, with no authentication required.
Most home routers rely on “protected by not being on the internet” as their only security. DNS rebinding destroys that assumption.
DNS Amplification: DDoS via DNS
DNS amplification exploits open DNS resolvers to amplify attack traffic by 50–100x. The attacker sends a small query spoofing the victim’s IP, and the resolver sends a much larger response to that victim, overwhelming their bandwidth without requiring significant botnet resources.
A single DNS ANY query (~40 bytes) can generate a 3,000+ byte response. Multiplied across thousands of open resolvers, the result is a massive volumetric DDoS.
Defences:
- Never run an open DNS resolver
- Implement BCP38 source address validation at the network edge
- Enable DNS Response Rate Limiting (RRL)
- Disable or minimise responses to ANY queries (RFC 8482)
AI-Driven DNS Attacks in 2026
The most significant shift in 2026 is the convergence of AI with DNS exploitation.
- AI-generated phishing infrastructure: ML models generate hundreds of near-identical lookalike domains that pass traditional brand-similarity checks
- Staged pre-positioning: Attackers register domain infrastructure weeks or months before activation. Spikes in newly observed domains precede phishing campaigns by 2-6 weeks.
- ML-evasive DGAs: Deep learning domain generation algorithms produce names statistically indistinguishable from legitimate traffic, defeating entropy-based detection
- Automated reconnaissance: AI scans DNS records at scale to identify misconfigured zones, forgotten subdomains, and exposed internal services faster than any human analyst
The defender’s response requires ML-powered DNS monitoring that evaluates domains in full context, query frequency, registration age, certificate transparency logs, and geographic patterns, rather than simple blocklists.
How to Detect DNS Attacks
Command-Line Checks
# Check your authoritative nameservers for unexpected changes
dig yourdomain.com NS +short
# Compare responses across global resolvers — inconsistency signals poisoning
dig @8.8.8.8 yourdomain.com A +short
dig @1.1.1.1 yourdomain.com A +short
dig @208.67.222.222 yourdomain.com A +short
# Detect tunneling — look for anomalously long subdomain queries in logs
grep -E ‘query: [a-zA-Z0-9+/]{50,}\.’ /var/log/named/query.log
Anomaly Reference Table
| Anomaly | Likely Attack |
| Sudden NS record change | Registrar/domain hijacking |
| Domain resolves to different IPs across resolvers | Cache poisoning |
| Spike in NXDomain responses | DGA malware C2 search |
| Base64-encoded subdomain queries | DNS tunneling/data exfiltration |
| Very short TTL (1–5 seconds) on your records | DNS rebinding preparation |
| High-volume TXT queries to an unknown domain | DNS tunneling C2 channel |
| Internal hosts querying external resolvers directly | Malware bypassing internal DNS |
DNS Security Checklist
Domain & Registrar
- Enable registrar lock (transfer lock) on all domains
- Enable MFA on your registrar account, use an authenticator app, not SMS
- Set up registrar alerts for any NS, A, or MX record changes
- Monitor NS records continuously and verify they match expected values
DNSSEC & Encrypted DNS
- Enable DNSSEC on all domains
- Verify DNSSEC validation: dig yourdomain.com A +dnssec
- Enable DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT) on endpoints
- Use a validating resolver: Cloudflare 1.1.1.1, Google 8.8.8.8, or Quad9 9.9.9.9
Email Authentication
- Publish SPF record for all sending domains
- Configure DKIM signing on outgoing mail
- Enforce DMARC at p=reject
- Implement BIMI for verified logo display in Gmail and Yahoo
Network & Resolver Hardening
- Never run an open DNS resolver
- Implement DNS Response Rate Limiting (RRL)
- Enable BCP38 source address validation at the network edge
- Block outbound DNS from endpoints to anything except your authorised resolvers
- Subscribe to certificate transparency monitoring for your domain
Conclusion
DNS remains one of the most critical and most overlooked components of internet security. In 2026, attackers exploit it through hijacking, spoofing, tunneling, rebinding, amplification, and, increasingly, AI-enhanced techniques that evade traditional detection.
The good news is that most of these attacks are detectable and preventable with the right foundations. Enable DNSSEC. Use DNS-over-HTTPS. Lock your registrar. Monitor your records. Enforce email authentication. And treat DNS logs as a frontline security signal, not background noise.
DNS security is not a set-and-forget task. It requires continuous vigilance, layered defences, and awareness of how the threat landscape evolves, starting with understanding the attacks described here.
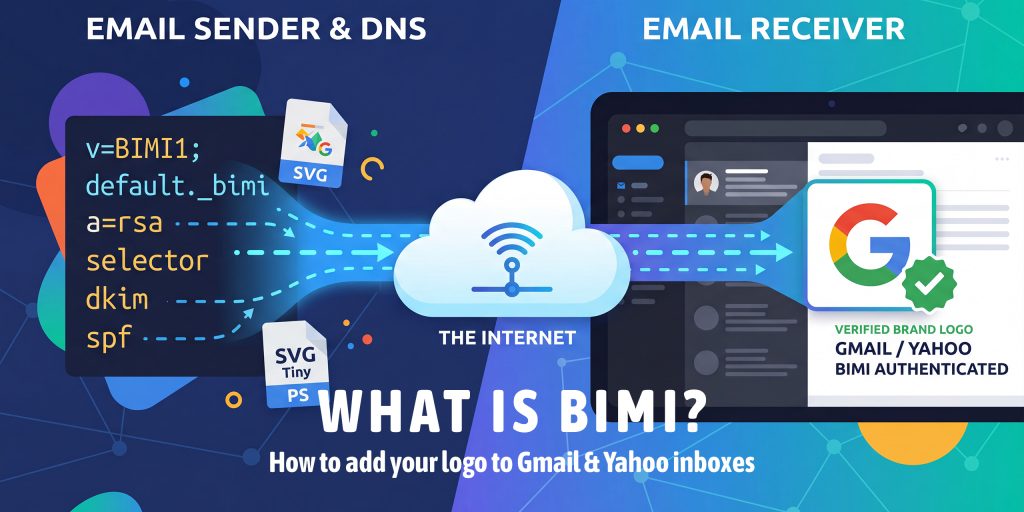
What is BIMI? How to Add Your Brand Logo to Gmail & Yahoo Inboxes
BIMI (Brand Indicators for Message Identification) is an email standard that lets you display your brand’s verified logo directly in the inbox, next to your email subject line, in Gmail, Yahoo Mail, Apple Mail, and other supporting providers. It requires DMARC enforcement (p=quarantine or p=reject) and, for Gmail and Apple Mail, a Verified Mark Certificate (VMC). BIMI turns email authentication into a visible trust signal that boosts open rates and protects your brand from impersonation.
What is BIMI?
BIMI stands for Brand Indicators for Message Identification. It is an open email specification published by the AuthIndicators Working Group that allows organizations to display a verified brand logo in the inbox avatar slot, the small image next to the sender name and subject line.
In plain terms: BIMI puts your logo in the inbox before your email is even opened. Instead of seeing a generic initial or a grey placeholder, your recipients see your real brand logo, verified and authenticated.
BIMI sits at the top of the email authentication stack. It builds on three lower-level protocols, SPF, DKIM, and DMARC, and adds a visual, human-readable layer of trust on top of them.
| Protocol | Checks | Visible to Recipients? | Required for BIMI? |
|---|---|---|---|
| SPF | Sender IP authorization | No | Yes (indirectly via DMARC) |
| DKIM | Message integrity signature | No | Yes (indirectly via DMARC) |
| DMARC | From: domain alignment + policy | No | Yes, must be enforced |
| BIMI | Brand logo display | Yes, logo in inbox | The reward layer |
The key insight: BIMI is not a standalone tool. It is the visible payoff for correctly implementing the full email authentication stack. You cannot shortcut to BIMI; the foundation must be solid first.
BIMI vs. Google Profile Photos: You may have seen sender avatars in Gmail that come from Google account profile photos or company logos set through Google Workspace. These are different from BIMI. BIMI logos are cryptographically verified against your domain via a Verified Mark Certificate; they cannot be faked or impersonated by another sender.
Why BIMI Matters in 2026
Email inboxes are more crowded and more dangerous than ever. AI-generated phishing emails now closely mimic legitimate brand communications. Recipients are increasingly skeptical of emails from brands they don’t immediately recognize visually.
BIMI addresses this from multiple angles simultaneously:
For Brand Trust & Recognition
- Instant visual recognition: Your logo appears before the email is opened, and recipients know it’s really you at a glance
- Verified authenticity: The VMC proves the logo belongs to your trademarked brand; it cannot be spoofed
- Reduced inbox anxiety: 53% of consumers say they’ve received legitimate brand emails they didn’t trust (Sinch). BIMI eliminates that doubt
For Email Performance
- Open rate lift: Research shows an average 10% increase in open rates for BIMI-enabled senders
- Inbox differentiation: Your email stands out visually against competitors who haven’t implemented BIMI
- Spam filter confidence: BIMI-enabled domains signal strong authentication hygiene, which can positively affect deliverability scoring
For Security
- Anti-impersonation: Attackers cannot display your verified logo without your VMC private key
- DMARC enforcement prerequisite: Getting to BIMI forces you to fully implement DMARC at p=reject, which protects your domain from spoofing entirely
- Domain reputation signal: Inbox providers treat BIMI-enabled domains as high-trust senders
2026 Competitive Reality: Fortune 500 companies are at 81.2% BIMI readiness. If your competitors’ logos show up in Gmail and yours don’t, that’s a visible trust gap. BIMI is moving from early-adopter advantage to table-stakes expectation for professional email senders.
DNS Records for ns1.dns-parking.com
How BIMI Works: Step by Step
When you send an email to a BIMI-supporting inbox provider, this is what happens behind the scenes:
- You send an email from your authenticated domain
- The receiving mail server checks SPF and DKIM; both must pass for your domain
- The server evaluates your DMARC policy; it must be p=quarantine or p=reject
- If DMARC passes, the server looks up your BIMI record at default._bimi.yourdomain.com
- The BIMI record contains a URL to your SVG logo and, optionally, your VMC certificate URL
- The inbox provider fetches your SVG logo from the URL in your BIMI record
- If a VMC is present, it is validated against your domain to confirm the logo is legitimately yours
- Your logo appears in the inbox next to your email, verified and authenticated
Why Providers Check DMARC First: Without DMARC enforcement, any attacker could publish a BIMI record claiming your logo. DMARC enforcement is the gate that proves you control the domain and all email from it is authenticated. BIMI without DMARC would be a spoofing attack vector; that’s why the requirement exists.
Which Inbox Providers Support BIMI?
BIMI support has expanded significantly since 2022. Here is the current state as of 2026:
| Inbox Provider | VMC Required? | DMARC Policy Needed | Notes |
| Gmail | Required | p=quarantine or p=reject | Requires VMC from DigiCert or Entrust. Largest user base, highest BIMI value. |
| Yahoo Mail | Optional | p=quarantine or p=reject | Supports self-asserted BIMI without VMC if the domain reputation is sufficient. |
| Apple Mail | Required | p=quarantine or p=reject | Requires VMC. Supported since iOS 16 / macOS Ventura. |
| Fastmail | Optional | p=quarantine or p=reject | Supports BIMI without VMC. |
| Cloudmark | Optional | p=quarantine or p=reject | Supports BIMI, VMC optional. |
| La Poste | Optional | p=quarantine or p=reject | French provider, BIMI, supported since Aug 2022. |
| Zone Webmail | Required | p=quarantine or p=reject | VMC required for logo display. |
| Outlook/M365 | Pending | N/A | Microsoft has announced BIMI support, but full rollout is still limited as of 2026. |
Practical priority: Focus on Gmail first, it has the largest user base and the clearest requirements. Yahoo is a strong second because you can display logos there without a VMC while you pursue Gmail support.
BIMI Requirements: What You Need Before You Start
BIMI has a clear prerequisite chain. Think of it as a checklist you work through from bottom to top:
- SPF record published: all sending services authorized on your root domain
- DKIM configured: every platform sending as your domain signs messages with DKIM
- DMARC published: and escalated to p=quarantine or p=reject (p=none does not qualify)
- DMARC pass rate consistently above 98%: check your aggregate reports
- SVG logo in SVG Tiny PS format: hosted at a permanent HTTPS URL
- VMC obtained (for Gmail & Apple Mail): from DigiCert or Entrust
- BIMI DNS TXT record published at default._bimi.yourdomain.com
Common Mistake: Jumping to BIMI Too Early: The most common BIMI setup failure is attempting it before DMARC is fully enforced. If your DMARC is at p=none, or your pass rate is below 95%, BIMI logos will not display in Gmail, even with a valid VMC. Complete the DMARC escalation path first, then pursue BIMI.
How to Run a Traceroute (tracert) Command
The Verified Mark Certificate (VMC) Explained
What is a VMC?
A Verified Mark Certificate (VMC) is a digital certificate, similar in concept to an SSL certificate, that cryptographically verifies that a logo belongs to the trademarked owner of a domain. It is issued by authorized Certificate Authorities (CAs) after validating your trademark registration.
The VMC is what makes BIMI trusted. Without it, any domain could claim any logo. The VMC proves that the logo in your BIMI record belongs to your organization’s registered trademark.
VMC Requirements
- Registered trademark: You must have a registered trademark (not just a pending application) for your logo in at least one major trademark jurisdiction (USPTO, EUIPO, UKIPO, CIPO, IP Australia, INPI, or NIPO)
- SVG Tiny PS logo: The logo must exactly match your trademarked image and be in SVG Tiny PS format
- Authorized CA: VMCs are currently issued by DigiCert (digicert.com/verified-mark-certificates) and Entrust (entrust.com)
- Domain ownership: You must prove control of the domain for which the VMC is issued
VMC Cost & Renewal
VMC certificates typically cost between $1,200–$1,500 USD per year from DigiCert or Entrust. They must be renewed annually. For organizations sending meaningful email volume, the open rate and brand trust improvements make this cost-effective, but for very small senders (under a few thousand emails/month), the ROI may not yet justify it.
What is a CMC?
CMC (Common Mark Certificate) is a newer alternative to VMC that does not require a registered trademark. It is supported by some providers (notably Apple Mail) and verifies brand identity through other means. As of 2026, CMC adoption among inbox providers is still growing. VMC remains the primary standard for Gmail support.
Strategy: Start with Yahoo, While Getting Your VMC: If you don’t have a VMC yet, don’t wait. Publish your BIMI record without the VMC certificate URL (omit the a= tag). Yahoo Mail and Fastmail will display your logo based on domain reputation alone. This gives you immediate BIMI benefits while your VMC application is in progress.
How to Prepare Your SVG Logo for BIMI
One of the most common BIMI failures comes from using an incorrect SVG format. BIMI doesn’t accept just any SVG; it requires a specific subset called SVG Tiny PS (Portable Secure). Here’s exactly what that means and how to get it right.
SVG Tiny PS Requirements
- Format: SVG Tiny 1.2, Portable/Secure profile (SVG Tiny PS)
- Shape: Must be a perfect square with equal width and height (e.g., 300×300 viewBox)
- Background: Must have a solid, opaque background; transparent backgrounds are not allowed
- No external references: No linked images, external fonts, JavaScript, animations, or raster images embedded inside
- Single file: Fully self-contained, all paths and shapes defined within the SVG file
- File size: Keep under 32KB for best compatibility
- MIME type: Must be served with Content-Type: image/svg+xml (not text/plain or application/xml)
What is NOT Allowed in BIMI SVGs
- Transparent or semi-transparent backgrounds
- Raster images (PNG, JPG) embedded inside the SVG
- JavaScript or scripting of any kind
- Animations (including CSS animations)
- External font references (@font-face with external URLs)
- Filters and effects (blur, drop-shadow, etc.)
- Linked external resources (xlink:href to external files)
How to Create a BIMI-Compliant SVG
Option 1: Adobe Illustrator:
- Create or open your Square logo in Illustrator
- Ensure the artboard is perfectly square
- Add a solid background rectangle if none exists
- Go to File → Save As → SVG → click More Options → set Profile to SVG Tiny 1.2
- Validate the output with a BIMI SVG validator
Option 2: Inkscape (free):
- Open your logo in Inkscape
- Set Document Properties to a square canvas
- Add a solid background rectangle
- File → Save As → SVG Tiny 1.2
- Manually review the XML to remove any disallowed attributes
Option 3: Professional BIMI SVG services:
Services like BIMI Inspector (bimigroup.org/creating-bimi-svg-logo-files) provide validation tools and guidelines. Some VMC providers (DigiCert, Entrust) offer SVG conversion assistance as part of the certificate process.
Hosting Your BIMI SVG
- URL must be HTTPS: plain HTTP will cause BIMI to fail silently
- No authentication required: the file must be publicly accessible without login or redirect
- No redirects: serve the SVG directly at the URL in your BIMI record
- Correct Content-Type header: Content-Type: image/svg+xml
- No hotlink protection: inbox providers’ servers must be able to fetch the file
- Stable URL: if you move the file, update your BIMI record. Broken logo URLs = no BIMI display
Step-by-Step: Add BIMI to Gmail
Confirm you have: (1) DMARC at p=quarantine or p=reject with pct=100, (2) DMARC pass rate consistently above 98%, check your DMARC aggregate reports, (3) SVG logo in SVG Tiny PS format hosted at an HTTPS URL, (4) VMC from DigiCert or Entrust with the .pem certificate file hosted at an HTTPS URL.
Step 1: Obtain Your VMC
- Go to DigiCert (digicert.com) or Entrust (entrust.com)
- Select ‘Verified Mark Certificate’ and begin the application
- Submit your trademark registration details (jurisdiction + registration number)
- Upload your SVG Tiny PS logo file for validation
- Complete domain validation (DigiCert will verify you control the domain)
- Wait for certificate issuance, typically 3–10 business days
- Download the .pem certificate file
Step 2: Host Your Certificate
- Upload your VMC .pem file to a stable HTTPS URL on your website
- Example: https://yourdomain.com/bimi/vmc.pem
- Ensure the file is publicly accessible with no authentication or redirect
- Confirm Content-Type is application/x-pem-file
Step 3: Host Your SVG Logo
- Upload your BIMI-compliant SVG logo to a stable HTTPS URL
- Example: https://yourdomain.com/bimi/logo.svg
- Test that the URL is publicly accessible in an incognito browser window
- Confirm Content-Type header is image/svg+xml
Step 4: Publish Your BIMI DNS Record
- Log in to your DNS provider (Cloudflare, Route 53, GoDaddy, Namecheap, etc.)
- Create a new TXT record with:
| Field | Value |
|---|---|
| Name / Host | default._bimi (some providers add your domain automatically; check their docs) |
| Type | TXT |
| Value | v=BIMI1; l=https://yourdomain.com/bimi/logo.svg; a=https://yourdomain.com/bimi/vmc.pem |
| TTL | 3600 (1 hour) or your provider’s default |
| DNS TXT record: default._bimi.yourdomain.com |
| v=BIMI1; l=https://yourdomain.com/bimi/logo.svg; a=https://yourdomain.com/bimi/vmc.pem |
Step 5: Verify with HasheTools
- Go to hashetools.com and open the BIMI Lookup tool
- Enter your domain name and click Check BIMI
- The tool will retrieve and validate: BIMI record syntax, SVG URL accessibility, VMC certificate validity, DMARC compliance
- Address any warnings or errors before sending a test email
Step 6: Send a Test Email to Gmail
- Send an email from your domain to a Gmail account you control
- Check the inbox; your logo should appear in the avatar circle next to the sender’s name
- Allow up to 24–48 hours for Gmail’s systems to pick up and cache your BIMI record
- If the logo doesn’t appear: use Gmail’s Postmaster Tools to check your domain reputation; low-reputation domains may not qualify even with a valid VMC
Step-by-Step: Add BIMI to Yahoo Mail
Yahoo Mail is the easiest path to BIMI because it supports logo display without a VMC, provided your domain has sufficient sending reputation with Yahoo’s filter systems.
Yahoo BIMI Without a VMC: You can display your logo in Yahoo inboxes by publishing a BIMI record with just the l= (logo URL) tag and no a= (VMC) tag. Yahoo evaluates your domain’s sending reputation and engagement history to decide whether to show the logo. This makes Yahoo the ideal first step in your BIMI rollout.
Step 1: Confirm DMARC Enforcement
Check your DMARC record using HasheTools DMARC Lookup. Confirm the policy is p=quarantine or p=reject. Yahoo will not show BIMI logos for domains at p=none.
Step 2: Prepare and Host Your SVG Logo
Follow the same SVG Tiny PS format requirements covered in Section 7. Host the SVG at a publicly accessible HTTPS URL with the correct Content-Type header.
Step 3: Publish Your BIMI Record (No VMC Required for Yahoo)
| DNS TXT record, default._bimi.yourdomain.com (Yahoo, no VMC) |
| v=BIMI1; l=https://yourdomain.com/bimi/logo.svg |
The a= tag (VMC URL) is optional for Yahoo. If you already have a VMC, include it; it won’t hurt. If you don’t have one yet, the record above is sufficient to request the Yahoo logo display.
Step 4: Build Yahoo Sending Reputation
Yahoo’s decision to display your BIMI logo is also influenced by your sending reputation with Yahoo’s filter systems. To build a strong reputation:
- Maintain low spam complaint rates (below 0.1% ideally)
- Send to engaged subscribers who open and click
- Honor unsubscribes promptly
- Use consistent sending volumes and patterns
- Warm up new sending IPs gradually
Step 5: Test and Monitor
- Send a test email from your domain to a Yahoo Mail account you control
- Check whether your logo appears next to your sender name
- If it doesn’t appear immediately, give it 7–14 days. Yahoo caches BIMI lookups and reputation signals, which take time to accumulate
- Use Yahoo Sender Support (sendersupport.yahoo.com) to check for deliverability issues affecting logo display
CNAME Lookup: How to Check, Verify, and Understand CNAME Records
Your BIMI DNS Record: Syntax & Examples
Full BIMI Record Syntax
| DNS TXT, default._bimi.yourdomain.com |
| v=BIMI1; l=https://yourdomain.com/bimi/logo.svg; a=https://yourdomain.com/bimi/vmc.pem |
| Tag | Example | Meaning |
|---|---|---|
| v=BIMI1 | v=BIMI1 | Required. Declares this is a BIMI record. Must be first. |
| l= | l=https://domain.com/logo.svg | URL to your SVG Tiny PS logo. Must be HTTPS. No redirects. |
| a= | a=https://domain.com/vmc.pem | URL to your VMC .pem file. Required for Gmail & Apple Mail. Omit for Yahoo-only. |
BIMI Record Examples
Full BIMI with VMC (Gmail + Yahoo + Apple Mail):
| DNS TXT: default._bimi.yourdomain.com |
| v=BIMI1; l=https://yourdomain.com/bimi/logo.svg; a=https://yourdomain.com/bimi/vmc.pem |
Yahoo-only BIMI (no VMC):
| DNS TXT: default._bimi.yourdomain.com |
| v=BIMI1; l=https://yourdomain.com/bimi/logo.svg |
Subdomain-specific BIMI (for newsletters sent from newsletter.yourdomain.com):
| DNS TXT: default._bimi.newsletter.yourdomain.com |
| v=BIMI1; l=https://yourdomain.com/bimi/newsletter-logo.svg; a=https://yourdomain.com/bimi/vmc.pem |
Temporarily disabling BIMI (while updating logo/VMC):
| DNS TXT: default._bimi.yourdomain.com |
| v=BIMI1; l= |
BIMI Record Name Format: The BIMI record must be published at exactly default._bimi.yourdomain.com, where ‘default’ is the selector (like DKIM selectors). Most deployments use ‘default’. Some DNS providers auto-append your domain; enter just ‘default._bimi’ as the host in that case. Check your DNS provider’s documentation.
How to Verify Your BIMI Record with HasheTools
After publishing your BIMI record, use HasheTools’ free tools to confirm everything is correctly configured:
| HasheTools Tool | What It Checks for BIMI |
|---|---|
| BIMI Lookup | Retrieves your BIMI DNS record. Validates l= and a= URLs are accessible. Checks VMC validity. Shows how the logo will appear. Flags errors. |
| DMARC Lookup | Confirms your DMARC policy is at p=quarantine or p=reject, the mandatory BIMI prerequisite. |
| DNS Lookup → TXT | View all TXT records on your domain to confirm the BIMI record is published and correctly formatted. |
| DKIM Lookup | Verifies DKIM is configured, required for DMARC to pass, which is required for BIMI to activate. |
| Blacklist Check | Confirms your sending IPs are not on spam blocklists, critical for maintaining the reputation that BIMI requires. |
| MTA-STS Lookup | Validates secure email transport, part of a complete email authentication setup that supports BIMI. |
Manual Verification Commands
You can also verify your BIMI record using command-line tools:
| Terminal: Check BIMI record with dig |
| dig TXT default._bimi.yourdomain.com +short |
| Terminal: Check BIMI record with nslookup |
| nslookup -type=TXT default._bimi.yourdomain.com |
Troubleshooting Common BIMI Problems
Logo Not Showing in Gmail
| Cause | Fix |
|---|---|
| DMARC is not in enforcement | Escalate DMARC from p=none to p=quarantine or p=reject. This is mandatory for Gmail. |
| No VMC or invalid VMC | Obtain a VMC from DigiCert or Entrust. Ensure the .pem file is hosted at the URL in your a= tag. |
| SVG not in SVG Tiny PS format | Re-export your SVG using the SVG Tiny PS profile. Use Adobe Illustrator or Inkscape. Validate with BIMI Inspector. |
| SVG served with the wrong MIME type | Check your web server config. The SVG must be served with Content-Type: image/svg+xml. |
| SVG URL requires authentication | Make the SVG URL publicly accessible without login, cookies, or redirects. |
| Domain reputation too low | Check Google Postmaster Tools. Build reputation by improving engagement and reducing spam complaints. |
| BIMI record not propagated | Wait up to 48 hours after publishing. Use HasheTools DNS Lookup to confirm propagation. |
Logo Not Showing in Yahoo
| Cause | Fix |
|---|---|
| DMARC is not in enforcement | Same as Gmail, p=none will not work. |
| Insufficient sending reputation | Send to engaged Yahoo users consistently over time. Keep spam complaints very low. |
| SVG format issues | Use the same SVG Tiny PS format requirements as Gmail. |
| BIMI record syntax error | Use HasheTools BIMI Lookup to check for syntax issues in your DNS record. |
VMC Validation Errors
- ‘Certificate not found at URL’: Ensure the a= URL in your BIMI record points directly to the .pem file with no redirect.
- ‘Certificate expired’: VMCs must be renewed annually. Check your expiry date and renew with DigiCert or Entrust
- ‘Logo does not match certificate’: The SVG logo in your l= tag must exactly match the logo embedded in your VMC. Reissue the VMC if the logo has changed
- ‘Domain not covered’: The VMC must be issued for the exact domain in your From: address. Wildcard coverage varies by CA
Use BIMI Inspector for Deep Validation: The BIMI Group (bimigroup.org) provides a free BIMI Inspector tool that validates your full BIMI setup, SVG format, DNS record, VMC, and DMARC in one check. Use it alongside HasheTools BIMI Lookup for comprehensive verification before launch.
BIMI FAQs
Do I absolutely need a VMC for BIMI?
You need a VMC to display your logo in Gmail and Apple Mail. Yahoo Mail and Fastmail support BIMI without a VMC, based on domain reputation. If you don’t have a trademark registration, you can still benefit from Yahoo BIMI while working toward VMC eligibility.
How long does BIMI setup take from start to finish?
If you already have DMARC at p=reject, the technical BIMI setup (SVG + DNS record) can be done in a day. Obtaining a VMC typically takes 3–10 business days, depending on trademark verification. If you need to escalate DMARC first, plan for 4–12 weeks for the full authentication journey.
Will BIMI affect my email deliverability?
BIMI itself doesn’t directly change deliverability scoring, but the DMARC enforcement required to enable it does. Fully enforced DMARC at p=reject, combined with proper SPF and DKIM alignment, significantly improves how inbox providers perceive your domain’s trustworthiness, which can positively impact inbox placement over time.
Can I use BIMI on subdomains?
Yes. Publish a BIMI TXT record at default._bimi.subdomain.yourdomain.com for emails sent from that subdomain. Each subdomain needs its own BIMI record and its own DMARC policy (unless the parent domain policy covers subdomains via the sp= tag).
What is the difference between BIMI and a Google Avatar?
Google Workspace profile photos and manually set sender avatars are informal; they can be set by anyone. BIMI logos are cryptographically verified through a VMC and can only be displayed when the domain passes DMARC authentication. A BIMI logo carries a trust verification that an avatar does not.
Can multiple domains use the same VMC?
No. A VMC is issued for a specific domain and covers exactly that domain (or optionally a wildcard). Each domain that sends BIMI-authenticated email needs its own VMC.
Do I need to do anything special in Gmail to enable BIMI?
No action is needed on the Gmail side. Gmail automatically checks for BIMI records when evaluating incoming emails from domains that pass DMARC. The setup is entirely on your domain’s DNS and certificate side.
How often do I need to update my BIMI record?
Only when something changes: if you update your logo, change the SVG URL, renew your VMC (annually), or switch VMC providers. BIMI records themselves don’t expire; only the VMC certificate does.
Conclusion
BIMI (Brand Indicators for Message Identification) is no longer just a “nice-to-have”; it’s becoming a standard for trusted email communication in 2026. By displaying your verified logo in inboxes like Gmail, Yahoo Mail, and Apple Mail, BIMI boosts brand recognition, improves open rates, and protects your domain from spoofing and phishing.
However, BIMI is the reward for a properly authenticated email setup: SPF, DKIM, and DMARC must be correctly configured and enforced before your logo can appear. For Gmail and Apple Mail, a Verified Mark Certificate (VMC) ensures your logo is cryptographically verified, while Yahoo and Fastmail allow BIMI without a VMC based on domain reputation.
In short, implementing BIMI signals to recipients and inbox providers that your emails are authentic and trustworthy, giving your brand a visible edge in crowded inboxes. Start with DMARC enforcement, prepare your SVG Tiny PS logo, obtain a VMC if needed, and publish your BIMI DNS record. The payoff is a stronger brand presence and a safer email experience for your audience.

SPF, DKIM, DMARC & BIMI: Complete 2026 Setup Guide
Google, Yahoo, and Microsoft now enforce email authentication for bulk senders. 83.9% of domains still have no DMARC record, making them prime targets for spoofing, phishing, and spam. This step-by-step guide covers every protocol you need: SPF, DKIM, DMARC, and BIMI.
What is Email Authentication?
Every time you send an email, receiving mail servers ask a simple question: Is this message really from who it claims to be? Without authentication, anyone can forge your domain in the From: field; this is how most phishing and business email compromise (BEC) attacks work.
Four DNS-based protocols work together to answer that question definitively:
| Protocol | What It Does | Where It Checks | Enforced By |
|---|---|---|---|
| SPF | Lists authorized sending IPs for your domain | Return-Path / envelope | Receiving mail server |
| DKIM | Cryptographically signs every outgoing message | DKIM-Signature header | Receiving mail server |
| DMARC | Ties SPF/DKIM to visible From: domain + reports | From: header alignment | Inbox providers (Gmail, etc.) |
| BIMI | Displays your brand logo in the inbox | BIMI DNS record + VMC | Gmail, Yahoo, Apple Mail |
Think of these as a security stack: SPF and DKIM authenticate the message, DMARC enforces a policy when they fail, and BIMI is the trust signal that rewards you for doing it right.
2026 Enforcement Update: Google & Yahoo require SPF + DKIM + DMARC for all senders of 5,000+ emails/day. Microsoft enforced similar rules from early 2025. Non-compliant messages are rejected at the SMTP level, not just filtered to spam.
SPF: Sender Policy Framework
What is SPF?
SPF is a DNS TXT record that publishes a list of IP addresses and servers authorized to send email on behalf of your domain. When a message arrives, the receiving server checks the sender’s IP against your SPF record. If the IP isn’t on the list, SPF fails.
Important limitation: SPF only checks the Return-Path / envelope sender, not the visible From: address your recipient sees. That’s why SPF alone doesn’t prevent spoofing. You need DMARC for full alignment.
How to Write an SPF Record
SPF records are DNS TXT records published on your root domain. Here’s the anatomy:
| DNS TXT record: @ (your root domain) |
| v=spf1 include:_spf.google.com include:sendgrid.net ip4:203.0.113.10 -all |
| Mechanism | Example | Meaning |
|---|---|---|
| v=spf1 | v=spf1 | Required, declares this is an SPF record |
| include: | include:_spf.google.com | Authorizes all IPs listed in that domain’s SPF record |
| ip4: | ip4:203.0.113.10 | Authorizes a specific IPv4 address or CIDR range |
| ip6: | ip6:2001:db8::/32 | Authorizes a specific IPv6 address or range |
| a | a:mail.example.com | Authorizes the A record IP of the given domain |
| mx | mx | Authorizes the MX record IPs of your domain |
| -all | -all | FAIL, reject all senders not listed (recommended) |
| ~all | ~all | SOFTFAIL, mark suspicious but deliver (use while testing) |
| ?all | ?all | NEUTRAL, no policy (avoid in production) |
SPF Setup Step-by-Step
- Log in to your DNS provider (Cloudflare, GoDaddy, Route 53, Namecheap, etc.)
- Create a new TXT record on your root domain (@)
- Set the value to: v=spf1 [your sending sources] -all
- List every service that sends email as your domain (your mail server, email marketing platform, CRM, support desk, etc.)
- Save and wait for DNS propagation (up to 48 hours)
- Verify using the HasheTools SPF Lookup tool
The 10-Lookup Limit: SPF records may not trigger more than 10 DNS lookups during evaluation. Each ‘include:’ counts as one lookup, and those includes often have their own includes. If you exceed 10, SPF fails with a PermError. Use SPF flattening tools to consolidate if needed.
Read Also: DNS Records for ns1.dns-parking.com
Common SPF Record Examples
Google Workspace users:
| DNS TXT: @ |
| v=spf1 include:_spf.google.com ~all |
Microsoft 365 users:
| DNS TXT: @ |
| v=spf1 include:spf.protection.outlook.com ~all |
Google Workspace + Mailchimp + custom mail server:
| DNS TXT: @ |
| v=spf1 include:_spf.google.com include:servers.mcsv.net ip4:203.0.113.10 -all |
DKIM: DomainKeys Identified Mail
What is DKIM?
DKIM adds a cryptographic digital signature to every outgoing email. The signature is added to the DKIM-Signature header and is verified by the receiving server using a public key stored in your DNS.
Unlike SPF, DKIM proves that the message content hasn’t been tampered with in transit. Even if an email passes through a mail relay or forwarding service, the DKIM signature remains valid, making it more resilient than SPF for complex mail flows.
How DKIM Works
- Your mail server signs each outgoing email using a private key stored on the server
- The signature is added to the DKIM-Signature email header
- The receiving server looks up your public key from a DNS TXT record at selector._domainkey.yourdomain.com
- The public key verifies the signature; if it matches, DKIM passes
- If the message was altered in transit, the signature won’t match, and DKIM fails
Your DKIM DNS Record
DKIM records follow this format:
| DNS TXT: selector._domainkey.yourdomain.com |
| v=DKIM1; k=rsa; p=MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA… |
| Field | Meaning |
|---|---|
| v=DKIM1 | Version, always DKIM1 |
| k=rsa | Key type, RSA (default) or ed25519 for modern servers |
| p=… | The base64-encoded public key, generated by your mail server or email provider |
| selector | A name you choose (e.g, ‘google’, ‘mail’, ‘s1’). Allows multiple DKIM keys per domain. |
DKIM Setup Step-by-Step
- Generate your DKIM key pair in your email service’s dashboard (Google Workspace, Microsoft 365, SendGrid, Mailchimp, etc.). They provide the public key and the selector name.
- Create a DNS TXT record at selector._domainkey.yourdomain.com and paste in the public key value they provide.
- Use 2048-bit RSA keys (recommended over 1024-bit for security).
- Save the DNS record and wait for propagation.
- Verify using the HasheTools DKIM Lookup tool by entering your domain and selector.
Security Best Practice: Rotate Your DKIM Keys: DKIM keys should be rotated every 6–12 months. This limits the window of exposure if a private key is ever compromised. Your email provider’s dashboard usually has a key rotation option. After rotation, update the DNS TXT record with the new public key and retire the old selector.
Read Also: How to Run a Traceroute (tracert) Command
DMARC: Domain-based Message Authentication
What is DMARC?
DMARC (Domain-based Message Authentication, Reporting, and Conformance) is the protocol that ties SPF and DKIM together and actually checks the visible From: address your recipient sees.
SPF and DKIM authenticate the message, DMARC enforces alignment. It tells receiving servers: if this message fails authentication, here’s what to do with it. And it sends you reports about every email sent from your domain, so you can see who’s using it.
DMARC Alignment Explained
DMARC passes when at least one of these is true:
- SPF alignment: The domain in the Return-Path (envelope sender) matches the visible From: domain
- DKIM alignment: The domain in the DKIM signature (d= tag) matches the visible From: domain
DMARC Record Structure
| DNS TXT: _dmarc.yourdomain.com |
| v=DMARC1; p=reject; rua=mailto:dmarc-reports@yourdomain.com; ruf=mailto:forensic@yourdomain.com; pct=100; adkim=s; aspf=s |
| Tag | Example | Meaning |
|---|---|---|
| v=DMARC1 | v=DMARC1 | Required, declares this is a DMARC record |
| p= | p=none / quarantine / reject | Policy: what to do with messages that fail DMARC |
| rua= | rua=mailto:reports@domain.com | Address for aggregate XML reports (daily summaries) |
| ruf= | ruf=mailto:forensic@domain.com | Address for forensic/failure reports (per-message) |
| pct= | pct=100 | Percentage of failing mail the policy applies to (100 = all) |
| adkim= | adkim=r or adkim=s | DKIM alignment: r = relaxed (default), s = strict |
| aspf= | aspf=r or aspf=s | SPF alignment: r = relaxed (default), s = strict |
| sp= | sp=reject | Policy for subdomains (if different from main domain) |
DMARC Policy Escalation: The Right Path
Never jump straight to p=reject. Follow this phased approach:
| Phase | DMARC Record | What Happens / When to Move On |
| Phase 1 (Weeks 1–4) | p=none | Monitor mode. Emails are delivered normally. Collect aggregate reports. Identify all sending sources. Move on when you understand your mail flow. |
| Phase 2 (Weeks 5–8) | p=quarantine; pct=25 | 25% of failing mail goes to spam. Gradually increase pct to 50 → 100 over 2–4 weeks. Move on when legitimate mail passes consistently. |
| Phase 3 (Weeks 9–12) | p=quarantine; pct=100 | All failing mail goes to spam. Monitor for 1–2 weeks. If no legitimate mail is affected, escalate. |
| Phase 4 (Final) | p=reject; pct=100 | Full enforcement. Failing mail is rejected at the SMTP level. Add sp=reject for subdomain coverage. You’re protected. |
Reading DMARC Aggregate Reports: DMARC sends you daily XML reports (rua) showing every IP address that sent email as your domain, how many messages passed or failed SPF/DKIM, and from which countries. Tools like HasheTools DMARC Lookup, or dedicated platforms like Postmark, EasyDMARC, or dmarcian, parse these into readable dashboards.
Read Also: What Is a DNS PTR Record?
BIMI: Brand Indicators for Message Identification
What is BIMI?
BIMI is the reward for doing email authentication right. Once your domain reaches DMARC enforcement (p=quarantine or p=reject), you can publish a BIMI DNS record that tells supporting inbox providers to display your brand logo next to your emails.
Supported by Gmail, Yahoo Mail, Apple Mail, Fastmail, and Cloudmark, BIMI gives your emails a verified checkmark-style visual trust signal before the recipient even opens them.
BIMI Requirements
- DMARC enforcement: p=quarantine or p=reject with pct=100, p=none does not qualify
- SVG logo: Your brand logo in SVG Tiny PS format, hosted at a stable HTTPS URL
- VMC (Verified Mark Certificate): Required by Gmail and Apple Mail. Optional for Yahoo, Fastmail. A VMC is issued by DigiCert or Entrust and validates your logo against your trademarked brand.
BIMI Record Structure
| DNS TXT: default._bimi.yourdomain.com |
| v=BIMI1; l=https://yourdomain.com/logo.svg; a=https://yourdomain.com/vmc.pem |
| Tag | Meaning |
|---|---|
| v=BIMI1 | Required, version tag |
| l= | URL to your SVG Tiny PS logo (must be HTTPS, correct MIME type: image/svg+xml) |
| a= | URL to your Verified Mark Certificate (.pem file), required for Gmail/Apple Mail |
BIMI Setup Step-by-Step
- Reach DMARC p=reject with consistent pass rates above 98%, BIMI is the final reward, not a shortcut
- Prepare your SVG logo in SVG Tiny PS format (specific SVG subset, use tools like Adobe Illustrator or Inkscape with the SVG Tiny PS export profile)
- Host the SVG at a permanent HTTPS URL with Content-Type: image/svg+xml. Redirects and authentication will cause failures.
- Obtain a VMC from DigiCert (digicert.com) or Entrust if you want Gmail support. Requires a registered trademark.
- Publish the BIMI TXT record at default._bimi.yourdomain.com
- Verify using the HasheTools BIMI Lookup tool
No Trademark? No VMC? Start with Yahoo. Yahoo Mail supports BIMI without a Verified Mark Certificate, provided your domain has sufficient sending reputation. If you don’t have a registered trademark yet, you can still benefit from BIMI in Yahoo inboxes while pursuing VMC for Gmail support.
Complete DNS Records Cheat Sheet
Here is a complete summary of all DNS records you need to publish, with format and location for each:
| Record | Name / Host | Type | Value / Format |
| SPF | @ (root) | TXT | v=spf1 include:your-provider ~all |
| DKIM | selector._domainkey | TXT | v=DKIM1; k=rsa; p=YOUR_PUBLIC_KEY |
| DMARC | _dmarc | TXT | v=DMARC1; p=reject; rua=mailto:you@domain.com |
| BIMI | default._bimi | TXT | v=BIMI1; l=https://domain.com/logo.svg; a=https://domain.com/vmc.pem |
| MTA-STS | _mta-sts | TXT | v=STSv1; id=20260401 |
| TLS-RPT | _smtp._tls | TXT | v=TLSRPTv1; rua=mailto:tls-reports@domain.com |
Troubleshooting Common Errors
SPF Errors
PermError: too many DNS lookups
Cause: More than 10 include: directives (counting nested lookups). Fix: Use SPF flattening to replace include: with direct IP4: ranges. Or reduce the number of sending services you authorize.
SPF Fails for Forwarded Emails
Cause: Email forwarding changes the envelope sender, breaking SPF alignment. Fix: This is expected behavior. DKIM survives forwarding, make sure DKIM is configured, and DMARC allows DKIM-only alignment.
SPF Record Not Found
Cause: The TXT record hasn’t propagated yet, or was published on the wrong host. Fix: Wait up to 48 hours. Verify you published on @ (root domain), not a subdomain.
DKIM Errors
DKIM Signature Verification Failed
Cause: Message body was modified in transit (by a mailing list, forwarding service, or anti-virus scanner). Fix: Ensure your mail server doesn’t modify messages after signing. Consider using l= tag to sign only part of the body.
No DKIM Signature Found
Cause: Your mail server isn’t signing outgoing messages. Fix: Check your email provider’s settings and ensure the DKIM signing option is enabled for your domain.
DMARC Errors
DMARC Fails Despite SPF and DKIM Passing
Cause: Alignment failure. SPF or DKIM pass, but the authenticated domain doesn’t match the visible From: domain. Fix: Ensure the d= tag in your DKIM signature matches your From: domain exactly. Use relaxed alignment (adkim=r) if using subdomains.
Legitimate Email Going to Spam After p=reject
Cause: A sending service (newsletter tool, CRM, support desk) isn’t aligned. Fix: Go back to p=none, review your DMARC aggregate reports, find the unauthorized source, and add it to your SPF record and configure DKIM signing through that service.
BIMI Errors
Logo Not Displaying in Gmail
Cause: No VMC, DMARC not in enforcement, or SVG format issues. Fix: Ensure DMARC is p=quarantine or p=reject. Get a VMC from DigiCert or Entrust. Validate SVG is in SVG Tiny PS format and hosted at an HTTPS URL with the correct MIME type.
Frequently Asked Questions
Do I need all four protocols (SPF, DKIM, DMARC, BIMI)?
For basic email security, SPF + DKIM + DMARC are essential. BIMI is optional but increasingly valuable for brand trust. Google and Yahoo require at least SPF + DKIM + DMARC for bulk senders. We recommend implementing all four in sequence.
How long does DNS propagation take?
Changes typically propagate globally within 15 minutes to 48 hours, depending on your TTL settings. Use HasheTools DNS Lookup to check live propagation status from multiple global resolvers.
Will p=reject break legitimate email?
Only if some of your sending services aren’t properly authenticated. That’s why the phased approach (starting at p=none) is critical. Never jump to reject without reviewing your DMARC reports first.
Can I have multiple DKIM keys?
Yes. Each DKIM key is identified by a selector prefix (e.g., google._domainkey, sendgrid._domainkey). You can have as many selectors as needed, one per sending service.
Does SPF protect against spoofing?
SPF alone does not prevent display-name spoofing (the visible From: address). SPF only checks the envelope sender. You need DMARC to enforce alignment between the envelope sender and the visible From: domain.
What is the difference between rua and ruf DMARC tags?
rua receives daily aggregate reports (XML summaries of all mail sources). Ruf receives forensic/failure reports (copies of individual messages that failed DMARC). RUF reports are more privacy-sensitive and not supported by all receivers.
Do subdomains inherit DMARC policy?
By default, the parent domain policy applies to subdomains. Use the sp= tag to set a separate subdomain policy (e.g., sp=reject). Subdomains used for sending also need their own SPF and DKIM records.
Conclusion
Email authentication is no longer optional; it’s a requirement. With Google, Yahoo, and Microsoft enforcing strict rules, domains without proper authentication are not just at risk of landing in spam; they’re being rejected before they even reach the inbox.
The solution is clear:
- SPF verifies who can send emails for your domain
- DKIM ensures your messages haven’t been tampered with
- DMARC enforces rules and protects your domain from spoofing
- BIMI rewards your setup with visible brand trust in the inbox
Together, these protocols create a complete email security and trust framework.
But the real takeaway is this:
Start with SPF and DKIM, move to DMARC enforcement, and then unlock BIMI as the final step.
Most domains still haven’t completed this journey, which means implementing it now gives you a massive advantage in deliverability, security, and brand visibility.

DNS Records for ns1.dns-parking.com: Complete Guide to DNS Parking & Nameservers
If you have looked up a domain’s nameservers and seen ns1.dns-parking.com in the results, you are in the right place. Maybe you are troubleshooting why a website is not loading, trying to understand what your Hostinger account is doing, or just curious what “DNS parking” actually means. This guide explains everything, from what ns1.dns-parking.com is to the actual DNS records behind it, how DNS parking works, why domains get parked, and exactly what steps to take if you need to move away from it.
What is ns1.dns-parking.com?
ns1.dns-parking.com is a nameserver, specifically the primary nameserver in a nameserver pair operated by Hostinger, one of the world’s largest web hosting companies. Its partner nameserver is ns2.dns-parking.com.
Together, ns1.dns-parking.com and ns2.dns-parking.com form Hostinger’s DNS parking service. When a domain’s nameservers are set to this pair, Hostinger’s DNS infrastructure takes control of that domain’s DNS zone, but instead of directing visitors to an active website, the domain is placed in a “parked” state, typically displaying a placeholder page.
You will encounter this nameserver in these common scenarios:
- You registered a domain through Hostinger, but have not yet connected it to a website
- A domain you are investigating has been recently purchased and not yet configured
- A Hostinger customer has let their hosting plan lapse, but kept the domain registered
- You are checking nameservers for troubleshooting purposes and want to know who controls the DNS
Key technical facts about ns1.dns-parking.com:
| Detail | Value |
| Hostname | ns1.dns-parking.com |
| IPv4 Address | 162.159.24.201 |
| IPv6 Address | 2400:cb00:2049:1::a29f:18c9 |
| Operator | Hostinger Operations, UAB |
| Partner NS | ns2.dns-parking.com (162.159.25.42) |
| Infrastructure | Cloudflare network (Anycast routing) |
| TTL | 172800 seconds (48 hours) |
Who owns dns-parking.com? (Hostinger)
The domain dns-parking.com is registered and operated by Hostinger Operations, UAB, a Lithuanian company and one of the largest web hosting providers globally, serving over 3 million customers across 150 countries.
WHOIS records confirm the following:
| WHOIS Field | Details |
| Registrar | HOSTINGER operations, UAB |
| IANA ID | 1636 |
| Registered On | August 6, 2019 |
| Expires On | August 6, 2026 |
| Status | Client Transfer Prohibited |
| Abuse Contact | abuse-tracker@hostinger.com |
| DNS Contact | dns@hostinger.com |
The nameservers themselves run on Cloudflare’s Anycast network, which is why the IP addresses (162.159.24.201 and 162.159.25.42) belong to Cloudflare’s IP range. Hostinger uses Cloudflare’s infrastructure to deliver high-performance, globally distributed DNS resolution for the millions of domains it manages.
This is the same relationship used by many large providers; Cloudflare provides the underlying network, while Hostinger operates the DNS zones under its own branded nameserver names.
Actual DNS Records for ns1.dns-parking.com
When you run a full DNS lookup on ns1.dns-parking.com or its parent domain, dns-parking.com, here are the records you will find:
NS Records (Nameserver Records)
dns-parking.com. NS ns1.dns-parking.com.
dns-parking.com. NS ns2.dns-parking.com.
These NS records define the authoritative nameservers for the dns-parking.com zone itself. The domain is self-referential; it uses its own nameservers.
A Records (IPv4 Addresses)
ns1.dns-parking.com. A 162.159.24.201
ns2.dns-parking.com. A 162.159.25.42
These are the glue records, IPv4 address records for each nameserver. Glue records are necessary when a domain uses nameservers that are subdomains of itself. Without these A records, DNS resolvers would face a circular dependency (they would need to look up ns1.dns-parking.com to find dns-parking.com, but would need dns-parking.com’s nameservers to look up ns1.dns-parking.com).
AAAA Records (IPv6 Addresses)
ns1.dns-parking.com. AAAA 2400:cb00:2049:1::a29f:18c9
ns2.dns-parking.com. AAAA 2400:cb00:2049:1::a29f:192a
IPv6 glue records that allow the nameservers to be reached over IPv6 connections. Both nameservers fully support IPv6, making them compatible with modern dual-stack network environments.
SOA Record (Start of Authority)
dns-parking.com. SOA ns1.dns-parking.com. dns.hostinger.com. (
Serial: [current]
Refresh: 14400
Retry: 3600
Expire: 604800
Minimum TTL: 300 )
The SOA record identifies ns1.dns-parking.com as the primary master nameserver for the dns-parking.com zone. The administrative contact email encoded in the RNAME field resolves to dns@hostinger.com, confirming Hostinger’s ownership. The refresh interval of 14,400 seconds (4 hours) means secondary nameservers check for zone updates every 4 hours.
Network Dispersal
The two nameservers are hosted on different C-class networks:
- ns1.dns-parking.com → 162.159.24.x network
- ns2.dns-parking.com → 162.159.25.x network
This geographic and network dispersal is a best practice (per RFC 2182) that prevents a single point of failure; if one nameserver or its network experiences an outage, the other continues to answer DNS queries.
What Is DNS Parking?
DNS parking (also called domain parking) is the practice of registering a domain name and placing it in a temporary, inactive state, pointing its nameservers to a parking service rather than to a live web server.
Think of it like buying a piece of land and putting up a “Reserved” sign. The land is yours; no one else can use it, but nothing has been built on it yet. In the internet world, your domain is “yours” the moment you register it, but DNS parking is the sign you put up while deciding what to build.
When a domain is parked using ns1.dns-parking.com:
- The domain is fully registered and owned
- No active website is being served at the domain
- Visitors typically see a placeholder page (a “coming soon” page, a simple holding page, or sometimes advertisements)
- The domain’s DNS zone is managed by Hostinger’s parking service
- Email may or may not be configured, depending on the MX records in the zone
DNS parking is extremely common. At any given moment, a large percentage of all registered domains on the internet are in some form of parked state.
How DNS Parking Works: Step by Step
Here is exactly what happens when a domain is parked at ns1.dns-parking.com:
Step 1: Domain Registration: A user registers a domain (e.g., mysite.com) through Hostinger or another registrar. Hostinger automatically sets the nameservers to ns1.dns-parking.com and ns2.dns-parking.com.
Step 2: DNS Delegation: The domain’s registry (for .com domains, this is Verisign’s servers) stores glue records pointing to Hostinger’s parking nameservers. When anyone queries mysite.com, the global DNS system directs them to ns1.dns-parking.com for answers.
Step 3: DNS Zone Created: Hostinger’s parking nameservers create a default DNS zone for mysite.com. This zone contains minimal records, typically just the NS and SOA records, and possibly an A record pointing to a Hostinger parking page IP.
Step 4: Placeholder Page Served: Any visitor who types mysite.com into their browser is directed to Hostinger’s parking page server. A generic placeholder page is displayed; the domain is “parked.”
Step 5: Domain Owner Activates: When the domain owner purchases a hosting plan, sets up their website, and points the domain to their server (either by changing nameservers or updating A records), the domain moves out of the parked state.
Why Is My Domain Pointing to ns1.dns-parking.com?
There are several common reasons you might find a domain using ns1.dns-parking.com:
- Newly registered domain, not yet connected to hosting. This is the most common reason. When you register a domain with Hostinger and have not yet set up hosting or pointed it to a server, Hostinger parks it by default. This is standard practice across the industry.
- Hosting plan expired or cancelled. If an active Hostinger hosting plan lapses and the domain registration continues, Hostinger may revert the domain’s nameservers to the parking configuration until the hosting is renewed or the domain is pointed elsewhere.
- Domain transferred to Hostinger management. If you moved a domain’s DNS management to Hostinger (without necessarily hosting a website there), the domain may be placed under the parking nameservers.
- Purchased a domain as a brand protection measure. Companies and individuals often register multiple domain variations (e.g., both .com and .net versions of their name) and park the extras to prevent cybersquatting. These secondary domains naturally end up parked.
- Domain awaiting development. The website is still being designed or built. Rather than display an error, the domain sits on the parking nameservers until the site is ready to launch.
What Does a Parked Domain Look Like?
When you visit a domain parked at ns1.dns-parking.com, you will typically see one of these pages:
Hostinger “Coming Soon” or Placeholder Page: A simple branded page indicating that the domain is registered with Hostinger and the website is not yet set up. This is the most common result for newly registered domains.
“Domain for Sale” Page: Some parked domains display a page indicating the domain is available for purchase, with contact details for the current owner.
Blank Page or DNS Error: If the DNS zone has no A record configured for the parked domain, browsers may display a “This site can’t be reached” error rather than a placeholder page, even though the domain itself is registered.
Advertisement Page: Some parking services monetise parked domains by displaying pay-per-click ads related to the domain name keywords. This is less common with Hostinger’s default parking, but it can be enabled.
Is ns1.dns-parking.com Safe?
Yes, ns1.dns-parking.com is a legitimate, trusted nameserver operated by Hostinger, one of the world’s most established web hosting companies. Seeing this nameserver when looking up a domain does not indicate anything malicious.
However, here are a few nuances worth understanding:
From a trust perspective, A domain parked at ns1.dns-parking.com is inactive. If you are considering doing business with a company whose website resolves to a parking page, that is worth investigating further; it may mean the business has not set up its website yet, or it could indicate the site has been taken down.
From a security perspective, the nameservers themselves are operated on Cloudflare’s infrastructure, which provides robust DDoS protection and reliable uptime. There is no inherent security risk from the nameserver configuration.
From an email perspective: If a domain is parked without MX records configured, emails sent to that domain will bounce. If you are trying to reach someone at an email address hosted on a parked domain, the messages may not be delivered. (See the email section below for more details.)
What to be cautious of: Phishing attacks sometimes use newly registered, parked-looking domains as a cover. Always verify the full context of a domain, its registration age, ownership, and content, before trusting it for sensitive communications.
DNS Parking vs. Domain Forwarding vs. Active Hosting
These three terms are often confused. Here is a clear comparison:
| Feature | DNS Parking | Domain Forwarding | Active Hosting |
| Website displayed | Placeholder/parking page | Redirects to another URL | Your actual website |
| Nameserver | Parking NS (e.g., ns1.dns-parking.com) | Can vary | Your hosting provider’s NS |
| Purpose | Hold domain, no active site | Redirect traffic elsewhere | Serve a live website |
| Email support | Possible but limited | Depends on setup | Full email support |
| DNS records needed | Minimal (NS, SOA, optional A) | A or CNAME + redirect rule | Full DNS zone (A, MX, TXT, etc.) |
| Typical cost | Domain registration fee only | Domain registration fee + redirect | Domain + hosting fees |
Domain forwarding is when a parked domain automatically redirects visitors to another URL, for example, forwarding myolddomain.com to mynewdomain.com. This differs from parking because there is an active redirect in place, not just a placeholder page.
How to Check If Your Domain Is Using ns1.dns-parking.com
There are several quick ways to check whether a domain is parked at ns1.dns-parking.com:
Method 1: Use HasheTools DNS Lookup
The fastest method is to use the HasheTools DNS Lookup Tool:
- Go to hashetools.com/tools/dns-lookup
- Enter the domain name you want to check
- Select NS as the record type (or use “All Records” to see everything)
- Click Lookup. If the NS records show ns1.dns-parking.com and ns2.dns-parking.com, the domain is parked with Hostinger.
Method 2: Use HasheTools All Records Tool
For a complete picture of all DNS records associated with a domain, use the HasheTools All Records Tool, which returns every record type (A, AAAA, NS, MX, TXT, SOA, CNAME) in a single lookup.
Method 3: Use nslookup (Command Line)
On any operating system, open a terminal or command prompt and run:
nslookup -type=NS yourdomain.com
Look for the NS record values in the output. If you see ns1.dns-parking.com, the domain is parked.
Method 4: Use dig (Linux/macOS)
dig NS yourdomain.com
Check the ANSWER SECTION for the NS record values.
Method 5: Use HasheTools WHOIS
The HasheTools WHOIS Lookup will show the domain’s registered nameservers, registration date, expiry date, and registrar, giving you a full picture of the domain’s current status.
How to Move Away from DNS Parking: Point Your Domain to a Website
If your domain is parked at ns1.dns-parking.com and you want to connect it to an active website, follow these steps.
Option A: Change Your Nameservers (Recommended for Hostinger Hosting)
This is the cleanest option if you are hosting your website with Hostinger or another provider.
Step 1: Log in to your Hostinger account (or wherever your domain is registered).
Step 2: Navigate to Domains > Manage and select the domain you want to update.
Step 3: Find the Nameservers section and click “Change Nameservers.”
Step 4: Enter the nameservers provided by your hosting provider. For example:
- Hostinger hosting: ns1.hostinger.com and ns2.hostinger.com
- Cloudflare: your assigned Cloudflare nameservers
- Other providers: use the nameservers they give you when you set up your hosting
Step 5: Save the changes. DNS propagation typically takes between 15 minutes and 48 hours. During this time, some visitors may still see the parked page while others see your new site, depending on which DNS servers they query.
Option B: Update A Records (Keep Using dns-parking.com Nameservers)
If you want to keep Hostinger’s parking nameservers but just update where the domain points, you can update the A record in the DNS zone:
Step 1: Log in to your Hostinger account and go to Domains > DNS / Nameservers.
Step 2: Find the A record for @ (your root domain) and edit it.
Step 3: Change the IP address to your web server’s IP address.
Step 4: Save the changes and wait for propagation.
Related read: Website IP Lookup
Common Problems with Parked Domains and How to Fix Them
Problem 1: Website shows parking page even after changing nameservers
Cause: DNS propagation has not completed yet, or your browser/ISP has cached the old DNS response.
Fix: Wait up to 48 hours for full propagation. In the meantime, try flushing your local DNS cache to force your computer to fetch the latest records.
Related read: How to Flush DNS and Clear DNS Cache
Problem 2: Domain shows “This site can’t be reached” instead of a parking page
Cause: The DNS zone for the domain has no A record configured, not even for the parking page.
Fix: Log in to Hostinger’s DNS management and verify that an A record exists for the root (@) of the domain. If not, add one pointing to your server IP, or contact Hostinger support to restore the default parking page configuration.
Problem 3: Email stopped working after the domain was parked
Cause: The parking DNS zone may not have the correct MX records configured, causing email delivery to fail.
Fix: Log in to Hostinger’s DNS management and check the MX records for your domain. Add or restore the correct MX records for your email provider. See the email section below for full details.
Problem 4: Nameservers changed, but nothing was updated
Cause: Nameserver changes require propagation time, and some DNS resolvers cache NS records aggressively due to high TTL values (48 hours in this case).
Fix: Use the HasheTools DNS Lookup Tool to check the current NS records being returned. If they have updated, the issue is local DNS caching; flush your cache and try again.
Problem 5: Someone else registered a similar domain, and it is parked
Cause: Domain name squatting or cybersquatting, someone registered a domain similar to yours for resale or other purposes.
Fix: Check the WHOIS data using HasheTools WHOIS Lookup to identify the owner and registration date. You may be able to contact the owner through WHOIS contact details or pursue a UDRP (Uniform Domain-Name Dispute-Resolution Policy) complaint if trademark infringement is involved.
DNS Parking and Email: What You Need to Know
DNS parking and email do not always mix well. Here is what to watch out for:
MX Records on Parked Domains
A domain’s MX records determine where emails sent to that domain are delivered. When a domain is parked at ns1.dns-parking.com, Hostinger may or may not configure default MX records in the parking zone.
If no MX records exist in the parking zone, emails sent to any address @yourparkeddomain.com will bounce, and the sending mail server will receive a “no mail exchanger” error.
Checking MX Records
Use the HasheTools DNS Lookup Tool with record type set to MX to check whether your parked domain has mail exchanger records configured.
Adding MX Records While Parked
If you need email to work while your domain is parked (for example, using Google Workspace or another email provider), you can add MX records to the Hostinger DNS zone without changing the nameservers:
- Log in to Hostinger and go to DNS management for your domain
- Add the MX records provided by your email provider (Google Workspace, Microsoft 365, Zoho, etc.)
- Add the corresponding SPF TXT record
- Save and allow propagation
Related read: Reverse DNS Does Not Match SMTP Banner
Benefits and Drawbacks of DNS Parking
Benefits of DNS Parking
Protect your brand: Registering and parking domain variations (e.g., .net, .org, .co versions of your .com domain) prevents competitors or bad actors from acquiring them for phishing, cybersquatting, or brand confusion.
Secure your domain while building: Park a domain while your website is being designed or developed, so the name is not taken by someone else in the meantime.
Low cost: Parked domains only require the annual domain registration fee, no hosting costs, and no server maintenance.
Passive income potential: Some parking services display relevant pay-per-click advertisements on parked domains, generating small amounts of revenue from organic traffic.
Flexibility: A parked domain can be redirected to an active website, pointed to a new server, transferred to a different registrar, or sold at any time. Parking gives you options.
Drawbacks of DNS Parking
No active website: Visitors see only a placeholder page, which provides no value and can give a poor impression of your brand.
Email limitations: Without MX records, email is non-functional. If you need email on the domain, you must configure MX records manually, even while parked.
Lost traffic and SEO value: If the domain previously had organic traffic or search engine rankings, parking it causes those rankings to disappear over time, as search engines index a placeholder page with no content.
Potential spam filter issues: Domains with no active website or configured email infrastructure can sometimes be associated with poor sender reputation, relevant if you plan to use the domain for email marketing in the future.
False sense of activity: Cybercriminals occasionally use freshly registered, parked-looking domains to create a veneer of legitimacy before activating a phishing campaign. Seeing a parked page is not always innocent.
Frequently Asked Questions
What does it mean when a domain uses ns1.dns-parking.com?
It means the domain is managed by Hostinger’s DNS parking service. The domain is registered and owned by someone, but it is not connected to an active website. Hostinger displays a placeholder page for any visitor who types the domain into a browser.
Is ns1.dns-parking.com the same as Hostinger’s regular nameservers?
No. Hostinger’s active hosting nameservers are typically ns1.hostinger.com and ns2.hostinger.com. The ns1.dns-parking.com nameservers are specifically for Hostinger’s domain parking service; they hold domains that are not yet connected to active hosting.
Can I use ns1.dns-parking.com and still have a working website?
Yes, but you need to manually update the DNS records. If you add a valid A record in the Hostinger DNS zone pointing to your web server’s IP address, your website will work even while the nameservers remain ns1.dns-parking.com. However, switching to your hosting provider’s dedicated nameservers is generally cleaner and more reliable.
How long does it take to unpark a domain?
Changing nameservers or updating DNS records typically takes between 15 minutes and 48 hours to propagate globally. The TTL on the parking nameservers’ NS records is 172,800 seconds (48 hours), so in the worst case, you may need to wait the full 48 hours for all DNS resolvers worldwide to pick up the change.
Why do ns1.dns-parking.com IP addresses belong to Cloudflare?
Hostinger operates its DNS parking service on top of Cloudflare’s Anycast network infrastructure. This means the physical servers handling DNS queries are part of Cloudflare’s global network, while Hostinger manages the DNS zones and configurations. This is a common and legitimate arrangement; many providers use Cloudflare’s infrastructure as the backbone for their DNS services.
Can I run email on a parked domain?
Yes, by configuring MX records in the parking zone. Log in to Hostinger’s DNS management, add the MX records for your email provider, and add the SPF TXT record. Email will work independently of whether the domain has an active website.
What is ns2.dns-parking.com?
ns2.dns-parking.com is the secondary nameserver in Hostinger’s parking nameserver pair. It works alongside ns1.dns-parking.com for redundancy. Its IPv4 address is 162.159.25.42. Both nameservers must be set for the parking configuration to work correctly; you should never set just one of the two.
Will parking a domain hurt my SEO?
If you are parking a previously active domain with existing search engine rankings, parking it will hurt your SEO over time, search engines will index a thin placeholder page with no content, and your existing rankings will gradually disappear. If you are parking a brand new domain that has never had a website, there is no SEO impact yet.
Conclusion
ns1.dns-parking.com is Hostinger’s primary parking nameserver, a reliable, Cloudflare-backed piece of DNS infrastructure that holds domains in a managed, inactive state until their owners are ready to connect them to active websites.
Understanding what it means when you see this nameserver is essential for:
- Domain troubleshooting: knowing why a website is not loading
- Email deliverability: understanding why emails to a domain may bounce
- Security investigations: assessing the status and ownership of a domain
- Website migration: knowing exactly what steps to take to move away from parking
Whether you are a Hostinger customer who needs to activate your domain, a developer investigating an unfamiliar nameserver, or a business owner protecting your brand with parked domains, this guide has given you the complete picture.
Ready to look up DNS records right now? Use the tools below to investigate any domain in seconds.

How to Run a Traceroute (tracert) Command: Complete Guide for Windows, Mac & Linux
If a website is loading slowly, your connection keeps dropping, or emails are not reaching their destination, a traceroute (or tracert on Windows) is one of the first tools any network administrator or IT professional reaches for. It shows you exactly which path your data takes across the internet, hop by hop, and pinpoints where problems occur.
This guide covers everything you need to know: what traceroute is, how it works, how to run it on Windows, Mac, and Linux, how to read the results, what all the common flags do, and how to troubleshoot the most frequent issues.
What Is Traceroute (tracert)?
Traceroute is a built-in network diagnostic command available on virtually every operating system. It traces the path that data packets take from your device to a destination, such as a website, server, or IP address, and shows you every router (or “hop”) those packets pass through along the way.
For each hop, traceroute reports:
- The hostname or IP address of that router
- The round-trip time (RTT) is measured in milliseconds, which is the time it took a packet to reach that hop and return.
Think of traceroute as a GPS tracker for your internet traffic. Instead of just telling you whether you reached your destination (which ping does), traceroute shows you the entire journey, every road, every intersection, and how long you spent at each one.
This makes it an invaluable tool for diagnosing:
- Slow website loading times
- Network bottlenecks and high latency
- Routing problems and suboptimal paths
- Packet loss at specific network points
- Whether a problem is on your end, your ISP’s end, or the destination server’s network
Traceroute vs. Tracert: What Is the Difference?
The short answer: they are the same tool with different names on different operating systems.
| Name | Operating System | Protocol Used by Default |
| tracert | Windows | ICMP (Internet Control Message Protocol) |
| traceroute | Linux | UDP (User Datagram Protocol) |
| traceroute | macOS | UDP (User Datagram Protocol) |
Both tools accomplish the same goal, mapping the hop-by-hop route from your device to a destination, but they differ slightly in the underlying network packets they send. Windows tracert uses ICMP Echo Requests (similar to the ping command), while Linux and macOS traceroute use UDP packets by default, though this can be changed with flags.
The practical impact is minimal for most troubleshooting scenarios, but it matters when dealing with firewalls: some networks block UDP packets used by Linux/macOS traceroute, while others block ICMP used by Windows tracert. If one fails, you can often switch protocols using command flags (covered below).
How Does Traceroute Work? (TTL and ICMP Explained)
Traceroute uses a clever technique built on a networking concept called Time-to-Live (TTL).
Every IP packet sent across the Internet contains a TTL value, a number that limits how many routers (hops) the packet is allowed to pass through before it is discarded. Each router that handles a packet decrements the TTL by 1. When the TTL reaches zero, the router discards the packet and sends back an ICMP “Time Exceeded” error message to the sender.
Traceroute exploits this mechanism to map each hop, one at a time:
Step 1: Traceroute sends a packet with TTL = 1. The very first router in the path decrements TTL to 0, discards the packet, and sends back a “Time Exceeded” message, revealing the first hop’s IP address and response time.
Step 2: Traceroute sends a packet with TTL = 2. The first router passes it through (TTL drops to 1), the second router decrements it to 0, discards it, and sends back its “Time Exceeded” message, revealing the second hop.
Step 3 onward: This continues, incrementing TTL by 1 each time, until the packet finally reaches the destination, which sends back a “Port Unreachable” or ICMP Echo Reply message, signalling the trace is complete.
By collecting the ICMP “Time Exceeded” responses from each router along the path, traceroute builds a complete, ordered map of every hop between your device and the destination, along with the round-trip time for each one.
When Should You Run a Traceroute?
Traceroute is most useful in these situations:
Website or application loading slowly: A traceroute to the server’s IP address will show you which hop is adding the most latency, whether it is your local network, your ISP, a transit provider, or the destination’s own network.
Connection intermittently dropping: Running traceroutes over time can reveal a specific hop where packet loss is occurring, pointing to a problematic router or link.
Cannot reach a website or server at all: Traceroute can show you exactly where in the path connectivity breaks down; the last successful hop before the trace stops is usually where the problem lies.
Emails being rejected or flagged: Network routing issues between your mail server and the recipient’s server can sometimes be diagnosed with a traceroute to the destination mail server’s IP.
ISP troubleshooting: Your ISP’s support team will often ask you to run a traceroute to their servers to help diagnose problems on their end.
Security investigations: Network and security professionals use traceroutes as part of reconnaissance and network mapping to understand the infrastructure between two points.
Related read: Reverse IP Address Lookup
How to Run Traceroute on Windows (tracert)
On Windows, the command is called tracert (not traceroute). It is built into every version of Windows, no installation required.
Method 1: Using Command Prompt
Step 1: Press Windows Key + R on your keyboard to open the Run dialog box.
Step 2: Type cmd and press Enter. The Command Prompt window will open.
Step 3: In the Command Prompt, type the tracert command followed by the domain name or IP address you want to trace:
tracert example.com
or using an IP address:
tracert 8.8.8.8
Step 4: Press Enter. The trace will begin immediately and output results line by line.
Step 5: Wait for the trace to complete. You will see a Trace complete. message when it finishes. It may take between 30 seconds and a few minutes, depending on the number of hops involved.
Method 2: Using Windows Search
Step 1: Click the Start button and type cmd in the search bar.
Step 2: Right-click on “Command Prompt” and select “Run as administrator” for full access.
Step 3: Type your tracert command and press Enter.
Sample Windows tracert Output
Tracing route to example.com [93.184.216.34]
over a maximum of 30 hops:
1 2 ms 1 ms 1 ms 192.168.1.1
2 12 ms 10 ms 11 ms 10.20.30.1
3 15 ms 14 ms 15 ms isp-gateway.net [96.120.40.245]
4 22 ms 20 ms 21 ms core-router.isp.net [96.110.175.85]
5 35 ms 34 ms 35 ms 93.184.216.34
Trace complete.
Pro tip: Run tracert 8.8.8.8 to check your path to Google’s DNS server; it is a reliable, always-online destination for testing your network path. See our guide to 8.8.8.8 for more.
How to Run Traceroute on macOS
On macOS, the command is traceroute, and it runs from the Terminal application.
Method 1: Using Terminal
Step 1: Open Terminal. The fastest way is to press Command + Space to open Spotlight, type Terminal, and press Enter.
Step 2: In the Terminal window, type:
traceroute example.com
or using an IP address:
traceroute 8.8.8.8
Step 3: Press Enter. Hops will appear one by one as the trace progresses.
Method 2: Using Network Utility (macOS Monterey and earlier)
On older versions of macOS:
Step 1: Open Applications > Utilities > Network Utility.
Step 2: Click the Traceroute tab.
Step 3: Enter the domain name or IP address in the text field.
Step 4: Click the Trace button.
Note: Network Utility was removed in macOS Monterey (12.x). Use the Terminal method instead.
macOS Traceroute Note on sudo
On some macOS configurations, traceroute may need administrator privileges to use certain protocols:
sudo traceroute example.com
Enter your Mac password when prompted.
How to Run Traceroute on Linux {#traceroute-linux}
On Linux, the command is traceroute. It may or may not be pre-installed depending on your distribution.
Step 1: Check if traceroute is installed
Open a terminal and type:
traceroute –version
If you see a version number, it is already installed. If you see “command not found,” proceed to Step 2.
Step 2: Install traceroute (if not installed)
Ubuntu / Debian:
sudo apt-get install traceroute
CentOS / RHEL / Fedora:
sudo yum install traceroute
Arch Linux:
sudo pacman -S traceroute
Step 3: Run the traceroute command
traceroute example.com
or:
traceroute 8.8.8.8
On some Linux distributions, raw socket operations may require root privileges:
sudo traceroute example.com
Linux ICMP mode (same as Windows tracert)
By default, Linux traceroute uses UDP. To switch to ICMP mode (matching Windows tracert behaviour):
sudo traceroute -I example.com
How to Run Traceroute on Android and iOS
Mobile devices do not have a built-in terminal for traceroute by default, but free apps make it easy.
Android
Install a free network utility app from the Google Play Store, such as “Network Analyzer” or “Ping & Net”. These apps include a traceroute function; simply enter the domain or IP address and tap the traceroute button.
iOS (iPhone / iPad)
Install a free app from the App Store, such as “Network Analyzer” or “HE.NET Network Tools”. Both include a visual traceroute function that maps hops on a world map alongside the traditional output.
Traceroute Command Flags and Options Explained
Both tracert (Windows) and traceroute (Linux/macOS) support additional flags that modify how the command runs.
Windows tracert Flags
| Flag | Description | Example |
| -d | Skips DNS resolution, shows IP addresses only, which speeds up the trace | tracert -d example.com |
| -h <MaxHops> | Sets the maximum number of hops (default: 30) | tracert -h 50 example.com |
| -w <timeout> | Sets the wait time in milliseconds before a hop times out (default: 4000ms) | tracert -w 1000 example.com |
| -4 | Forces IPv4 | tracert -4 example.com |
| -6 | Forces IPv6 | tracert -6 example.com |
Full Windows tracert syntax:
tracert [-d] [-h MaximumHops] [-w timeout] [-4] [-6] target
Linux/macOS traceroute Flags
| Flag | Description | Example |
| -n | No DNS resolution, shows IPs only, faster trace | traceroute -n example.com |
| -m <hops> | Sets the maximum number of hops (default: 30) | traceroute -m 50 example.com |
| -w <seconds> | Wait time before timeout at each hop | traceroute -w 5 example.com |
| -I | Uses ICMP instead of UDP (same as Windows tracert) | sudo traceroute -I example.com |
| -T | Uses TCP SYN packets, useful for bypassing firewalls | sudo traceroute -T example.com |
| -p <port> | Specifies destination port | traceroute -p 80 example.com |
| -q <queries> | Number of probes per hop (default: 3) | traceroute -q 5 example.com |
| -4 / -6 | Force IPv4 or IPv6 | traceroute -4 example.com |
How to Read Traceroute Output
Once the trace completes, you will see output that can look overwhelming at first glance. Here is how to interpret every part of it.
Sample Output
Tracing route to hashetools.com [104.21.30.125]
over a maximum of 30 hops:
1 2 ms 1 ms 2 ms 192.168.1.1
2 10 ms 9 ms 11 ms 10.20.0.1
3 15 ms 14 ms 15 ms isp-gateway.example.com [96.120.40.245]
4 22 ms 21 ms 23 ms core1.isp.net [96.110.175.85]
5 45 ms 44 ms 47 ms ae-3.r21.nycmny01.us.bb.gin.ntt.net [129.250.6.97]
6 * * * Request timed out.
7 55 ms 54 ms 56 ms 104.21.30.125
Trace complete.
Column-by-Column Breakdown
Column 1 – Hop Number: The sequential number of each router in the path. Hop 1 is almost always your local router (gateway). The final hop is the destination server.
Columns 2, 3, 4 – Response Times (ms): Three separate round-trip time measurements in milliseconds. Traceroute sends three packets to each hop for reliability. These three values tell you:
- If all three are similar, that hop’s latency is stable
- If values vary wildly, there may be congestion or instability at that hop
- Lower is better; under 100ms is generally good, over 200ms is high
Column 5 – Hostname / IP Address: The domain name (if DNS resolved it) and/or the IP address of the router at that hop.
What Different Latency Values Mean
| Response Time | Interpretation |
| 1–20 ms | Excellent, local network or very nearby |
| 20–100 ms | Normal for domestic routing |
| 100–200 ms | Acceptable for international routes |
| 200–400 ms | High latency, investigate this hop |
| 400ms+ | Very high, likely a problem or geographic distance |
Identifying a Problem Hop
The key to reading traceroute output for troubleshooting is watching for a sudden jump in latency. If hops 1–5 show 20ms and hop 6 suddenly shows 200ms, and stays high for all subsequent hops, hop 6 is where the problem is occurring.
If latency is high at one hop but drops back to normal at the next hop, that particular router simply de-prioritises ICMP responses, and the delay is not a real problem.
What Do Asterisks (* * *) Mean in Traceroute?
You will often see rows of three asterisks in traceroute output:
6 * * * Request timed out.
Asterisks mean that no response was received from that hop within the timeout period. This does not always indicate a problem. Here is what different asterisk patterns mean:
Asterisks at one hop, then normal results resume: The router at that hop is configured to not respond to ICMP or UDP probe packets (firewalls and security-hardened routers commonly do this). The path is still working normally, the router is just silent.
Asterisks at every hop from a certain point onwards: This is the serious case. It usually means:
- The path is broken at or after the last successful hop
- A firewall is blocking all further responses
- The destination server or network is unreachable
Asterisks only at the last hop: The destination server itself may be blocking ICMP responses while still serving traffic normally on other ports (HTTP/HTTPS). Try accessing the website. If it loads, the asterisks are just firewall-filtered probes, not a real issue.
What to check based on where asterisks appear:
- Hops 1-3: The problem is likely on your local network or with your router
- Hops 4-8: Your ISP’s network may be having issues
- Hops 9 onward: The problem is either with a transit provider or with the destination’s network
- Final hop only: The destination server is likely filtering ICMP
Traceroute vs. Ping: What Is the Difference?
Ping and traceroute are both network diagnostic tools, and they complement each other well.
| Feature | Ping | Traceroute |
| What it tests | Whether the destination is reachable | The full path to the destination, hop by hop |
| Information returned | Round-trip time, packet loss | Each router in the path has per-hop latency |
| Identifies bottleneck location | No | Yes |
| Typical use case | Quick connectivity check | Diagnosing where exactly a problem occurs |
| Speed | Very fast | Slower (traces every hop) |
When to use ping: When you want to quickly check if a server is online and measure basic latency.
When to use traceroute: When you know there is a problem, and you need to identify exactly where in the network path it is happening.
Related read: Website IP Lookup
Common Traceroute Problems and What They Mean
Problem 1: Trace stops at hop 1 (your local router)
What it means: Your device cannot reach even the first hop, your own gateway/router. The problem is on your local network.
What to check: Reboot your router, check your network cable or Wi-Fi connection, and verify your local IP configuration.
Problem 2: Trace stops after a few hops at your ISP
What it means: Your traffic is reaching your ISP but not going any further. This is typically an ISP-side routing issue.
What to do: Contact your ISP with the traceroute output as evidence. The output clearly shows where the path breaks.
Problem 3: Extremely high latency at a specific hop
What it means: A router in the path is overloaded, geographically distant, or de-prioritizing probe packets.
What to check: If latency remains high at all subsequent hops, too, that hop is genuinely problematic. If subsequent hops are normal, the router is simply deprioritising ICMP, and it is not a real problem.
Problem 4: Destination unreachable / trace never completes
What it means: The destination is offline, has a firewall blocking the protocol, or the route does not exist.
What to check: Try the trace with a different protocol (use -I flag on Linux to switch to ICMP, or -T for TCP). Also, check if the destination website loads in a browser; if it does, the server just filters ICMP probes.
Problem 5: “Destination net unreachable” at hop 1
What it means: Your default gateway (router) has no route to the destination network.
What to check: This often indicates a routing table issue. Check your router’s configuration or contact your ISP.
Problem 6: Trace works from your device but not from the destination
What it means: The path may be asymmetric; internet traffic does not always take the same route in both directions. Issues may only appear in one direction.
What to do: Run a traceroute from the destination server back to your IP (this is what a reverse traceroute does). Some online tools offer this capability.
Related read: Reverse IP Address Lookup
How to Save Traceroute Results to a File
When troubleshooting network issues, especially when sharing results with your ISP, hosting provider, or IT team, you will want to save the output to a text file.
Windows: Save the tracert to a File
tracert example.com > C:\tracert-results.txt
This saves the results to a file called tracert-results.txt on the C: drive. You can open this file in Notepad or any text editor.
To save AND see the results in real time at the same time:
tracert example.com | tee C:\tracert-results.txt
macOS / Linux: Save traceroute to a File
traceroute example.com > traceroute-results.txt
The file will be saved in whichever directory your terminal is currently in. To see where that is, type pwd before running the command.
Sharing Traceroute Results
When sending results to your ISP or support team, include:
- The tracert/traceroute output (full text)
- Your public IP address
- The destination you traced to
- The date and time the trace was run
- A brief description of the problem you are experiencing
You can quickly check your public IP using the HasheTools My IP Address Tool and get detailed information about any IP using the HasheTools IP Lookup Tool.
Frequently Asked Questions
Is traceroute the same as tracert?
Yes, they are the same diagnostic tool. Tracert is the name Microsoft uses on Windows, while traceroute is the name used on Linux and macOS. Both map the hop-by-hop path your data takes to a destination.
How many hops is normal for a traceroute?
A typical domestic traceroute to a nearby server shows between 5 and 15 hops. International routes can show 20–30 hops. If you reach the default maximum of 30 hops without arriving at the destination, it usually means the destination is unreachable or heavily firewalled.
Why does my traceroute show asterisks (* * *)?
Asterisks mean a particular hop did not respond within the timeout period. This is often caused by firewalls or routers that are configured not to respond to ICMP/UDP probe packets. If subsequent hops respond normally, the asterisks are generally not a problem.
Can traceroute damage or harm a network?
No. Traceroute sends very small, standard network packets and does not harm networks in any way. It is a completely safe, read-only diagnostic tool.
Why does traceroute show different results each time I run it?
Internet routing is dynamic. Routers constantly adjust paths based on traffic load, network conditions, and routing table updates. Running a traceroute twice in quick succession may show slightly different paths; this is normal. For accurate troubleshooting, run multiple traces and look for consistent patterns.
What does “Request timed out” mean at every hop?
If every single hop after a certain point shows “Request timed out,” the path is broken at that point. The last responsive hop is where the problem likely originates. If all hops from the very beginning time out, you may have a local network or firewall issue blocking the tool entirely.
Can I run a traceroute on a domain name or only an IP address?
Both work. You can use either a domain name (e.g., tracert example.com) or an IP address (e.g., tracert 8.8.8.8). When you use a domain name, traceroute automatically resolves it to an IP address first.
What is a visual traceroute?
A visual traceroute is a graphical representation of the standard traceroute output, often showing hops plotted on a world map with geographic locations derived from IP geolocation data. It makes it easier to visualise the physical routing path your data takes across the internet.
Why does the latency suddenly drop in the middle of my traceroute?
Some routers prioritise traffic forwarding over generating ICMP responses. This means a router might appear to have high latency in a traceroute output even though it is actually forwarding traffic efficiently. If latency drops back down at subsequent hops, the apparent spike at that hop is not a real problem; it is just a router that responds to probe packets slowly while processing real traffic quickly.
Conclusion
The traceroute (or tracert on Windows) command is one of the most powerful and practical tools in any network troubleshooter’s toolkit. Whether you are investigating a slow website, hunting down packet loss, diagnosing email delivery issues, or simply curious about how your data travels across the internet, traceroute gives you a clear, hop-by-hop map of the path your data takes.
The key things to remember:
- Windows uses tracert, Linux and macOS use traceroute
- Each line of output = one router (hop) in the path
- The three numbers per hop are round-trip times in milliseconds
- Asterisks mean a hop did not respond, which is not always a problem
- A sudden spike in latency that stays high across subsequent hops = real issue
- Save your output to a file when sharing with support teams
Ready to go deeper? Use the HasheTools DNS Lookup Tool to check DNS records for any domain you are tracing, or use the HasheTools IP Lookup Tool to get detailed information about any IP address that appears in your traceroute output.

What Is a DNS PTR Record? Complete Guide to Reverse DNS Lookup
If you’ve ever wondered why your perfectly written emails end up in a spam folder, or why your mail server gets flagged during an SMTP test, there’s a good chance a DNS PTR record is at the heart of the issue. This guide breaks down everything you need to know about PTR records: what they are, how they work, why they matter, and how to check, create, and troubleshoot them.
What Is a DNS PTR Record?
A DNS PTR record (short for Pointer record) is a type of DNS record that maps an IP address back to a domain name. It is essentially the reverse of an A record, which maps a domain name to an IP address.
Think of it this way: the regular DNS system works like a phonebook where you look up a name to find a number. A PTR record works like a reverse phonebook; you start with the number (IP address) and look up who it belongs to (domain name). This process is called a reverse DNS lookup (or rDNS).
Simple definition: A DNS PTR record answers the question: “What domain name is associated with this IP address?”
PTR records are not used for general website browsing. Instead, they play a critical behind-the-scenes role in email delivery, network security, server logging, and spam prevention.
PTR Record vs. A Record: What Is the Difference?
Understanding a PTR record becomes easy once you compare it with the DNS A record, which most website owners are already familiar with.
| Feature | A Record | PTR Record |
| Direction | Domain → IP address | IP address → Domain |
| Lookup type | Forward DNS lookup | Reverse DNS lookup |
| Where it’s stored | Your domain’s DNS zone | Reverse DNS zone (.in-addr.arpa) |
| Who controls it | Domain owner | IP address owner (ISP or hosting provider) |
| Primary use | Website resolution | Email verification, logging, and security |
Example:
- A record: mail.example.com → 192.0.2.10
- PTR record: 192.0.2.10 → mail.example.com
Both records should point to each other. When they do, this is called Forward-Confirmed reverse DNS (FCrDNS), and it is a key trust signal for email servers.
How Does a DNS PTR Record Work?
Here is a step-by-step breakdown of how a PTR record lookup works:
- A mail server receives an incoming email from IP address 192.0.2.10.
- To verify the sender’s identity, the receiving server performs a reverse DNS lookup on 192.0.2.10.
- The DNS system looks up the PTR record for the reverse IP address 10.2.0.192.in-addr.arpa.
- The PTR record returns the associated domain name: mail.example.com.
- The receiving server then does a forward DNS lookup on mail.example.com to confirm it points back to 192.0.2.10.
- If both lookups match, the server accepts the email as coming from a legitimate, verified source.
If the PTR record is missing, mismatched, or misconfigured, the receiving server may reject or flag the email as spam.
What Is a Reverse DNS Lookup?
A reverse DNS lookup is the process of resolving an IP address into its associated domain name, using the PTR record stored in the DNS system.
It is the exact opposite of a standard (forward) DNS lookup:
- Forward DNS lookup: You type example.com into your browser → DNS returns 192.0.2.1
- Reverse DNS lookup: You query IP 192.0.2.1 → DNS returns example.com
Reverse DNS lookups are used for:
- Email verification: to confirm the identity of a sending mail server
- Security auditing: to map IP addresses found in network logs to human-readable domain names
- Spam filtering: to check whether the sending IP is associated with a known, legitimate domain
- Network troubleshooting: to identify the source of traffic or connections in server logs
You can run a reverse DNS lookup instantly using the HasheTools DNS Reverse Lookup Tool. Just enter any IP address and get the PTR record result in seconds.
PTR Record Format Explained (IPv4 and IPv6)
The way PTR records are stored in DNS is a bit different from how you might expect. The IP address is written backwards, and a special domain suffix is appended.
IPv4 PTR Record Format
For an IPv4 address like 192.0.2.255, the PTR record is stored as:
255.2.0.192.in-addr.arpa
The IP octets are reversed, and .in-addr.arpa is appended. This naming convention exists because DNS domains are organized from most specific (left) to most general (right), and reversing the IP address preserves this hierarchical structure.
IPv6 PTR Record Format
IPv6 PTR records work the same way but are more complex. For the IPv6 address 2001:db8::1, the PTR record is stored under:
1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.8.b.d.0.1.0.0.2.ip6.arpa
The IPv6 address is fully expanded, reversed digit by digit, and .ip6.arpa is appended instead of .in-addr.arpa.
What Is .arpa and Why Is It Used?
The .arpa top-level domain is a special domain used for managing network infrastructure in DNS. It is the oldest top-level domain on the internet, named after ARPA (Advanced Research Projects Agency), which created ARPANET, the precursor to the modern internet. The subdomain in-addr. arpa is specifically reserved for reverse DNS lookups of IPv4 addresses.
What Is FCrDNS (Forward-Confirmed Reverse DNS)?
FCrDNS stands for Forward-Confirmed reverse DNS, sometimes also called Full-Circle reverse DNS. It is a verification process that checks whether a PTR record and an A record are consistent with each other.
Here is how FCrDNS verification works:
- A reverse DNS lookup is performed on an IP address – it returns a domain name via the PTR record.
- A forward DNS lookup is then performed on that domain name – it should return the original IP address.
- If both match, the FCrDNS check passes, and the IP and domain are legitimately associated.
Why does FCrDNS matter?
FCrDNS is used by many email servers and security systems as a trust signal. A passing FCrDNS check indicates that:
- The domain owner and IP address owner are the same entity (or at least aware of each other)
- The server is operating transparently and following internet best practices
- The email is much less likely to be spam
If your PTR record exists but your A record does not point back to the same IP, FCrDNS will fail, and your emails may still be treated as suspicious.
Why Does a PTR Record Matter?
You might be thinking: “I don’t run a mail server, do I even need a PTR record?” For most regular website owners and users, PTR records operate entirely in the background. But if you fall into any of the following categories, they are critical:
1. Email Deliverability
This is the biggest use case. Mail servers at Gmail, Outlook, Yahoo, and other providers routinely perform reverse DNS lookups on every incoming email. If your sending IP has no PTR record, or a mismatched one, your emails are at high risk of being rejected or routed straight to spam. This is especially true for businesses running their own mail servers.
2. Anti-Spam Filtering
Spam filters assign a “spam score” to incoming emails based on dozens of signals. A missing or mismatched PTR record is a significant negative signal. Most enterprise anti-spam systems (including SpamAssassin) actively penalize emails from IPs with no reverse DNS.
3. Server Logging and Network Monitoring
System logs often record only IP addresses. When administrators need to investigate traffic, security incidents, or network activity, PTR records allow them to translate those raw IP addresses into readable domain names, making troubleshooting and forensic analysis far easier.
4. Server Identity and Trust
When servers connect, not just for email, but for other protocols, PTR records are used to verify the identity of the connecting server. This is a fundamental layer of trust in the internet infrastructure.
5. Cybersecurity Investigations
Security researchers, penetration testers, and network analysts use PTR lookups as part of reconnaissance and investigation workflows. Knowing which domain is associated with a given IP helps identify malicious actors, trace attack origins, and map network infrastructure.
PTR Records and Email Deliverability
Email deliverability is where PTR records have the most direct, visible impact. Here is a detailed look at how they affect your email:
How Receiving Mail Servers Use PTR Records
When an email arrives, the receiving mail server performs the following sequence:
- It checks the sender’s IP address.
- It performs a reverse DNS lookup to find the PTR record for that IP.
- It checks whether the PTR record resolves to a domain name.
- It performs a forward lookup on that domain name to confirm it matches the original IP (FCrDNS check).
- It compares the result against the SMTP banner that the sending server presented.
If any of these steps fail, no PTR record, wrong domain, mismatched A record, or SMTP banner mismatch, the email may be rejected, quarantined, or marked as spam.
Related read: Reverse DNS Does Not Match SMTP Banner
PTR Records and Spam Filters
Many popular anti-spam systems, including those used by major email providers, use reverse DNS as a filtering criterion:
- No PTR record = high suspicion of spam
- Generic PTR (e.g., ip-192-0-2-10.hosting.example.com) = moderate suspicion
- Properly configured PTR pointing to your domain = trust signal
PTR Records and Email Authentication (SPF, DKIM, DMARC)
PTR records work alongside, but are separate from, SPF, DKIM, and DMARC. While those protocols authenticate the email content and domain, PTR records authenticate the sending server’s IP address. Together, they form a comprehensive email authentication stack.
PTR Records vs. Other DNS Record Types
Here is how PTR records compare to other common DNS record types:
| Record Type | Function | Direction |
| A record | Map the domain to an IPv4 address | Forward (domain → IP) |
| AAAA record | Maps the domain to an IPv6 address | Forward (domain → IPv6) |
| PTR record | Maps an IP address to a domain | Reverse (IP → domain) |
| CNAME record | Aliases one domain to another | Forward (domain → domain) |
| MX record | Specifies the mail server for a domain | Forward (domain → mail server) |
| TXT record | Stores text data (SPF, DKIM, DMARC, etc.) | N/A |
| SOA record | Stores administrative info about a DNS zone | N/A |
Related read: DNS Records for google.com Explained
How to Check a PTR Record
There are several ways to check the PTR record for an IP address.
Method 1: Use HasheTools DNS Reverse Lookup
The easiest method is to use the HasheTools DNS Reverse Lookup Tool:
- Go to hashetools.com/tools/dns-reverse
- Enter the IP address you want to look up
- Click “Lookup”
- The tool will return the PTR record (domain name) associated with that IP
Method 2: Use the nslookup Command
On Windows, macOS, or Linux, open a terminal or command prompt and run:
nslookup 192.0.2.10
Or for a more targeted reverse lookup:
nslookup -type=PTR 10.2.0.192.in-addr.arpa
Method 3: Use the dig Command (Linux/macOS)
dig -x 192.0.2.10
The -x flag tells dig to perform a reverse lookup automatically. Look for the ANSWER SECTION in the output; it will show the PTR record.
Method 4: Use HasheTools SMTP Test
If you want to check PTR records specifically for your mail server and verify FCrDNS, use the HasheTools SMTP Test Tool. It will flag any PTR mismatches and SMTP banner issues automatically.
How to Create or Set Up a PTR Record
This is where PTR records differ significantly from all other DNS records. You cannot create a PTR record in your domain’s DNS settings (e.g., in Cloudflare, Namecheap, or GoDaddy). PTR records are controlled by whoever owns the IP address block, typically your ISP or hosting provider.
Step-by-Step: Setting Up a PTR Record
Step 1: Find your mail server’s IP address
Log in to your hosting control panel or run nslookup mail.yourdomain.com to find the IP address of your mail server.
Step 2: Identify who controls that IP
- If you host on a VPS or dedicated server (e.g., AWS, DigitalOcean, Vultr, Linode), the cloud provider controls the reverse DNS.
- If you use a shared hosting plan, your hosting company controls it.
- If you have a direct ISP-allocated IP range, your ISP controls it.
Step 3: Contact your provider or use their control panel
Many modern cloud providers allow you to set PTR records directly:
- AWS: Go to EC2 > Elastic IPs > Edit reverse DNS
- DigitalOcean: Rename your Droplet to the full hostname. DigitalOcean automatically creates the PTR record
- Vultr: Go to your server’s settings and find “Reverse DNS.”
- Linode/Akamai: Network tab > Reverse DNS
- Shared hosting: Submit a support ticket with your hosting provider
Step 4: Enter the correct PTR value
The PTR record value should be the fully qualified domain name (FQDN) of your mail server, for example: mail.yourdomain.com
Step 5: Create the matching A record
Make sure that mail.yourdomain.com has an A record pointing back to the same IP address. This completes the FCrDNS configuration.
Step 6: Verify the PTR record
After the DNS propagation period (usually 15 minutes to a few hours), verify the PTR record using the HasheTools DNS Reverse Lookup or the dig -x command.
Common PTR Record Mistakes and How to Fix Them
Mistake 1: Missing PTR Record
Symptom: Emails are being rejected or going to spam. SMTP tests show “No PTR record found.”
Fix: Contact your hosting provider or ISP and request a PTR record for your mail server’s IP address.
Mistake 2: Generic or Default PTR Record
Symptom: Your PTR record resolves to something like ip-192-0-2-10.us-east-1.compute.internal instead of your domain.
Fix: Update the PTR record via your cloud provider’s control panel (see the setup steps above) to point to your actual mail server hostname.
Mistake 3: PTR Record and A Record Mismatch (FCrDNS Failure)
Symptom: PTR record exists but FCrDNS check fails. The domain in your PTR record does not have a matching A record pointing back to the IP.
Fix: Ensure that the domain name in your PTR record has a corresponding A record pointing to the correct IP. Both records must match.
Mistake 4: SMTP Banner Mismatch
Symptom: SMTP test shows “Reverse DNS does not match SMTP banner.”
Fix: Update your mail server’s hostname (the value in the SMTP greeting/banner) to match the domain in your PTR record. In Postfix, this is the myhostname setting in /etc/postfix/main.cf.
Related read: Reverse DNS Does Not Match SMTP Banner
Mistake 5: Multiple PTR Records for One IP
Symptom: Inconsistent reverse lookups; some tools return different results.
Fix: Only one PTR record should exist per IP address. Remove any duplicates.
Mistake 6: Using a Dynamic IP Address
Symptom: PTR record keeps becoming invalid as the IP changes.
Fix: PTR records should only be used with static IP addresses. If your server has a dynamic IP, request a static IP from your provider before configuring a PTR record.
PTR Record Best Practices
Follow these guidelines to ensure your PTR records are configured correctly and deliver maximum benefit:
- Always configure a PTR record for every mail server IP. This is considered a basic Internet standard for email servers. Missing PTR records are a major red flag for spam filters.
- Make the PTR record match your mail server’s SMTP banner. The hostname your mail server announces when connecting to other servers must match what your PTR record resolves to.
- Ensure FCrDNS passes. Your PTR record should resolve to a domain, and that domain’s A record must point back to the same IP. Both lookups must agree.
- Use a meaningful, domain-specific hostname. Instead of a generic hostname, use something like mail.yourdomain.com. This builds trust and is easier to recognize in logs.
- Use only one PTR record per IP. Multiple PTR records for a single IP create ambiguity and can cause inconsistent behavior.
- Only use static IPs for PTR records. Dynamic IP addresses change over time, making PTR records unreliable.
- Regularly audit your PTR records. Use tools like HasheTools DNS Reverse Lookup to periodically check that your PTR records are correct and still match your A records.
- Keep TTL values reasonable. A TTL of 300–3600 seconds is standard for PTR records. Too high a TTL means changes propagate slowly; too low may cause unnecessary DNS query load.
Frequently Asked Questions
Do I need a PTR record for my website?
Not necessarily. PTR records are primarily needed for mail servers. If you only run a website and use a third-party email provider (like Google Workspace or Microsoft 365), those providers handle PTR records on your behalf. You only need to configure PTR records yourself if you operate your own mail server.
Who controls PTR records?
PTR records are controlled by the owner of the IP address block, not the domain owner. This is typically your ISP, cloud provider, or hosting company. To set up a PTR record, you must contact whoever issued your IP address.
Can I have multiple PTR records for one IP?
It is technically possible but strongly discouraged. Best practice is to have exactly one PTR record per IP address. Multiple PTR records create ambiguity and can confuse mail servers and spam filters.
What happens if my PTR record is missing?
If your mail server has no PTR record, many receiving mail servers will reject your emails outright or deliver them to the spam folder. It is one of the most impactful configuration issues for email deliverability.
How long does it take for a PTR record to propagate?
PTR record changes typically propagate within 15 minutes to a few hours, depending on the TTL set by your provider and the caching behavior of DNS resolvers worldwide.
What is the difference between a PTR record and reverse DNS?
They are closely related. Reverse DNS is the process of resolving an IP address to a domain name. A PTR record is the specific DNS resource record that makes reverse DNS possible. In other words, PTR records are the mechanism by which reverse DNS lookups are answered.
Can I check someone else’s PTR record?
Yes. You can perform a reverse DNS lookup on any public IP address using HasheTools DNS Reverse Lookup or command-line tools like dig -x or nslookup.
Is a PTR record the same as an rDNS record?
Yes. PTR record and rDNS record are the same thing. “rDNS” stands for reverse DNS, and the PTR (Pointer) record is the DNS record type used to enable reverse DNS lookups.
Conclusion
A DNS PTR record is a small but powerful piece of internet infrastructure. While regular users never interact with it directly, it plays an essential role in email deliverability, spam prevention, server logging, and network security.
If you run a mail server, a missing or misconfigured PTR record can silently destroy your email deliverability, causing your messages to be rejected or flagged as spam by major providers like Gmail, Outlook, and Yahoo. Getting your PTR record right and ensuring FCrDNS passes is one of the most effective steps you can take to protect your sender reputation.
Ready to check your PTR record right now? Use the HasheTools DNS Reverse Lookup Tool to instantly look up the PTR record for any IP address and verify that your reverse DNS is configured correctly.

IP Addresses for Facebook.com: Complete Facebook IP Lookup & DNS Analysis Guide
In the modern internet era, understanding the IP addresses of popular websites like Facebook is essential for IT professionals, web developers, network administrators, and even curious internet users. Every website on the internet, including Facebook.com, is hosted on servers identified by unique IP addresses. These IP addresses can be IPv4, IPv6, or associated with CNAME (Canonical Name) records.
In this guide, we will walk you through everything you need to know about Facebook’s IP addresses, how to look them up, verify them, and use tools like HasheTools to perform accurate DNS analysis.
What Is an IP Address?
An IP (Internet Protocol) address is a unique string of numbers that identifies a device or server on the Internet. Every website has at least one IP address associated with its domain name, which enables computers and servers to communicate.
- IPv4: Standard IP format, e.g., 57.144.222.1.
- IPv6: A newer format that accommodates more addresses, e.g., 2a03:2880:f36f:1:face:b00c::25de.
Facebook, being one of the largest social media platforms in the world, uses multiple IP addresses to distribute traffic efficiently across its global server network.
Why Knowing Facebook’s IP Address Is Useful
Understanding the IP addresses of Facebook.com can be helpful in multiple scenarios:
- Network Troubleshooting: If Facebook is not loading, checking the IP address can help identify whether the issue is local, with the ISP, or with Facebook’s servers.
- DNS Analysis: IT administrators may need to verify DNS configurations or troubleshoot routing issues.
- Firewall and Security Setup: Organizations may need to allow or block specific IP ranges for access control.
- Performance Monitoring: Knowing the IP helps in monitoring latency and server response times.
How to Find Facebook’s IP Addresses
There are multiple ways to find the IP addresses of Facebook, ranging from online tools to command-line methods. One of the easiest methods is to use HasheTools, an all-in-one DNS lookup and IP analysis platform.
Using HasheTools for Facebook IP Lookup
HasheTools provides a fast and accurate way to check the IP addresses of any website, including Facebook.
Steps:
- Open HasheTools.com.
- Navigate to the Website to IP Lookup Tool.
- Enter facebook.com in the input field.
- Click Check or Lookup.
- HasheTools will display all IP addresses associated with Facebook, including IPv4, IPv6, and any relevant CNAME records.
This method is beginner-friendly and eliminates the need for command-line knowledge.
Using Command-Line Tools for Facebook IP Lookup
If you prefer using built-in tools, here are the steps for Windows, macOS, and Linux:
Windows
- Open Command Prompt.
- Run the command:
nslookup facebook.com
- The output will show Facebook’s IPv4 and, if available, IPv6 addresses.
macOS and Linux
- Open Terminal.
- Run the command:
dig facebook.com A
dig facebook.com AAAA
- These commands will return all the IPv4 (A records) and IPv6 (AAAA records) addresses for Facebook.com.
Example of Facebook IP Addresses
Here is a real-world example of Facebook IP addresses (as of recent DNS lookup):
IPv4 Addresses:
- 57.144.222.1
(This may vary depending on your location and DNS server.)
IPv6 Addresses:
- 2a03:2880:f36f:1:face:b00c::25de
Note: Facebook uses multiple IP addresses for load balancing, regional distribution, and redundancy. The exact IPs may vary when you check using HasheTools or other DNS lookup services.
Understanding DNS Records for Facebook
Besides IP addresses, Facebook.com also uses several DNS records to ensure smooth performance:
- A Record: Maps the domain to an IPv4 address.
- AAAA Record: Maps the domain to an IPv6 address.
- CNAME Record: Aliases one domain to another (used for subdomains or services).
- MX Record: Handles email routing.
- TXT Record: Provides verification or security information.
- NS Record: Lists the authoritative DNS servers for the domain.
Using HasheTools, you can easily perform a full DNS lookup for Facebook and check all associated records in one place.
Why Facebook Uses Multiple IP Addresses
Facebook serves billions of users across the globe, which requires a distributed infrastructure. Multiple IP addresses allowed:
- Load Balancing: Traffic is distributed among multiple servers to reduce latency and server overload.
- Geo-Targeting: Users are routed to the nearest data center for faster loading.
- Redundancy: If one server fails, others take over to ensure uninterrupted service.
Checking Facebook IP addresses periodically using tools like HasheTools helps IT admins and enthusiasts understand this global infrastructure.
Troubleshooting Facebook Connectivity Using IP Addresses
Sometimes, Facebook may fail to load due to DNS or network issues. Here’s how IP addresses help:
- Ping Test: Test connectivity to a specific Facebook IP.
- Traceroute: Identify network hops and latency issues.
- DNS Verification: Confirm that your ISP or network is correctly resolving Facebook.com.
With HasheTools, you can quickly check both IPs and DNS configuration to diagnose problems.
Frequently Asked Questions
1. What is the IP address of Facebook?
Facebook’s IP addresses are distributed. Common IPv4 example: 57.144.222.1. IPv6: 2a03:2880:f36f:1:face:b00c::25de. For the most accurate and up-to-date IPs, use HasheTools.
2. Can Facebook IP addresses change?
Yes, Facebook frequently updates IPs for load balancing, regional distribution, and maintenance. Always perform a fresh lookup for accurate results.
3. How can I use Facebook IP addresses safely?
IP addresses should only be used for network monitoring, troubleshooting, or security setups. Never attempt unauthorized access to Facebook servers.
4. Can I track users on Facebook using their IP address?
No. User privacy is protected by Facebook, and IP addresses visible from your network are only for server connectivity, not individual users.
Final Thoughts
Checking and understanding Facebook’s IP addresses is essential for network troubleshooting, security setups, and DNS analysis. Using reliable tools like HasheTools simplifies this process, allowing you to access up-to-date IPs, verify DNS records, and analyze CNAMEs efficiently.
Whether you are a network professional, developer, or internet enthusiast, regularly using HasheTools to look up Facebook IP addresses ensures you stay informed and can resolve connectivity issues quickly.
Start your Facebook IP lookup today with HasheTools and monitor DNS changes in real-time!
Stay Updated
Get the latest articles and tutorials delivered to your inbox
